There are some whataboutism vibes to Microsoft writing about Mac ransomware, but this is a really good post on various techniques used by ransomware (and malware in general) on macOS https://www.microsoft.com/en-us/security/blog/2023/01/05/unraveling-the-techniques-of-mac-ransomware/
(Edit: this blog post was a little bit too much based on the great work of Patrick Wardle so Microsoft, rightly, took it down.)
Unraveling the techniques of Mac ransomware - Microsoft Security Blog
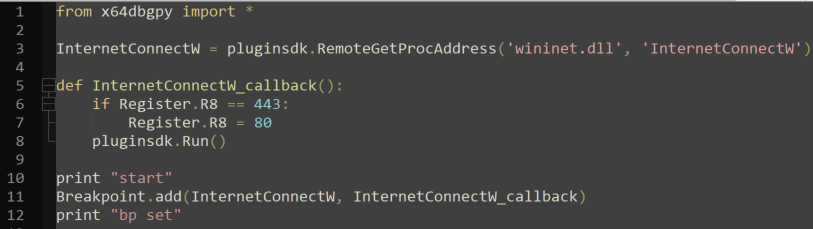
Understanding how Mac ransomware works is critical in protecting today’s hybrid environments. We analyzed several known Mac ransomware families and highlighted these families’ techniques, which defenders can study further to prevent attacks.