IT security in the 90s ...
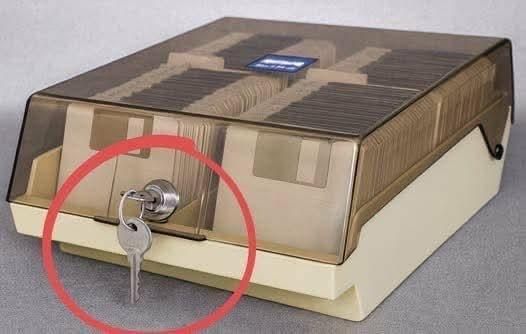
I bought a 3.5” USB floppy drive a year ago to get things off the disks I had in a couple of boxes like that. So far, none of the ones I’ve tried have been readable.
We used to be a proper country.
We landed men on the Moon using less memory than a single floppy disk and less processing power than a smartphone. Just so AI can burn 10 acres of forest with every poem and painting it generates from stolen art for the decadent amusement of bored bourgeois, while poor people work as janitors and fast-food clerks. "Would you like flies with this BS?"
@purrperl @drukac @Natasha_Jay important thing about landing on the moon though was that those machines were supported by a massive team of smart people (including the human computers who Buzz Aldrin called out as trusting then with his life)
The machines today are designed to replace humans.
Yeah, those were much anticipated, but the first batch bombed, because the engineers forgot to make the Sun roof standard with the ejectable seats, and now legal has to pay all those families, and we have to pay legal, and you have to pay us, so the next model will be ready soon, costlier than the last one.
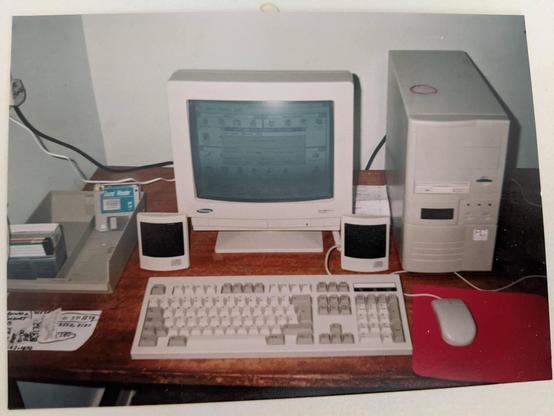
@D4lt0n @Natasha_Jay the Turbo Button did something if it was properly wired to the motherboard. It would change the CPU frequency if I correctly recall. The display was just a normal 7-segment and you could decide what to show with jumpers. Most PCs used the CPU clock if possible (66 for a 486Dx2) or HI/LO, because those fit in the two digits you could set (later cases came w 3 digits as seen on the pic)
But it did work! My first job was putting generic PCs together at a local computer shop.
The Windows 3 netBEUI network didn’t distinguish between what was on your computer and the rest of the network or the internet, once it was available. It was all directly accessible.
SNMP ( "Simple" Network Management Protocol ) was so simple, that it did not have any security. Anyone across the Internet could reach out and check your CPU load or take its temperature.
No way. This is news to me! 😵
Absolutely. Originally, anyone on the network had full read/write/modify to your full Windows file system. That’s what initially promoted the development of 3rd party firewalls. The first serious one was ZoneAlarm, which was essential equipment until Microsoft finally added firewall functionality to Windows XP, and even then it wasn’t very good.
I was spoiled, sitting behind a GNU/Linux campus-wide firewall at ( https://stevens.edu/ ). Soon gravitated towards the FOSS world, never plumbed the murky world of closed source. If one can clone & improve the capabilities of any closed technology, why bother studying its precious innards?
As a kid, I would take broken devices apart to investigate. By the time I diagnosed the issue, I would be daydreaming of a better version of the device, leaving this one in pieces.
yours had a lid? posh.
@Natasha_Jay Well, it’s probably safer than now, when you see the number of data breaches today.
Good luck hacking remotely these floppies now :D
Hatte ich 2 davon.
Yeah good luck hackers opening that from the other side of the continent 😂
Ow, wait, the whole case...
@Natasha_Jay Isn't that the same key for multi devices with bad locks?
Was a 751 if I remember. Same key for my RV's kitchen access cover.
@Natasha_Jay I can't think of anyone really protecting their disks with the lock, these things were primarily dust covers.
Besides, I can get one open with a paper clip in like 5 seconds.
In the 90s that was the whole Internet.
the unironically effective part of this was not actually labeling the floppies.
... and I always removed the locks. 🤷♂️
 🇪🇺
🇪🇺