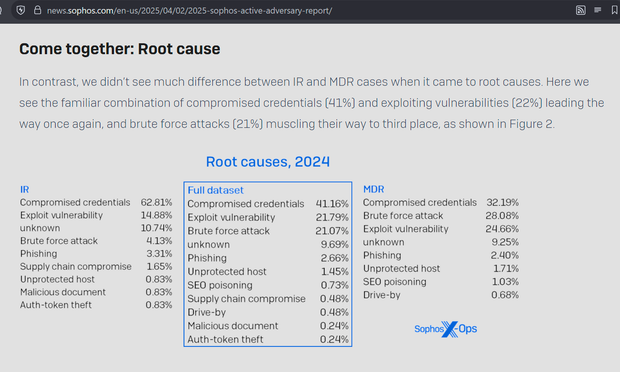
The 2025 Sophos Active Adversary Report is out.
I thread these every year as, personally, I think yearly IR and MDR reports are the best source of data for defenders on _real world_ threats.
https://news.sophos.com/en-us/2025/04/02/2025-sophos-active-adversary-report/
Key take aways for me:
- Despite what you read from scare vendors, ransomware dwell time (initial access to deployment) is still measured days.
It is not hopeless and by active monitoring you *can* stop attackers.

 🇺🇦
🇺🇦