Nowy, kosmiczny odcinek mojego podcastu "What the Fox says" jest już dostępny!
Dzisiejsze wydanie zdominowały tematy pozaziemskie, ale nie zabrakło też twardych, ziemskich realiów technologicznych. Sprawdźcie, o czym opowiadam w tym odcinku:
* Rewolucja w astrofizyce: Przyglądam się nowym odkryciom Kosmicznego Teleskopu Jamesa Webba. Układ WL20 rzuca wyzwanie dotychczasowym modelom fizycznym, a nowe dane mogą w końcu wyjaśnić zagadkę powstawania supermasywnych czarnych dziur we wczesnym wszechświecie.
* Nowa era napędów i misji: Omawiam sukcesy testów zaawansowanego napędu plazmowego NASA (AEPS) oraz technologie kriogeniczne Blue Origin – to technologie, które skrócą podróż na Marsa i pomogą nam przetrwać księżycową noc.
* Bitwa o suwerenność cyfrową: Analizuję projekt rosyjskiej konstelacji satelitarnej Razvet, która ma być odpowiedzią na Starlinka, oraz przytaczam dramatyczny apel twórcy Mistral AI o przyszłość europejskiej sztucznej inteligencji.
* Technologiczny "deskilling": Zastanawiam się, czy bezkrytyczne poleganie na automatyzacji i AI nie prowadzi nas prostą drogą do erozji poznawczej i utraty zdolności krytycznej oceny sytuacji.
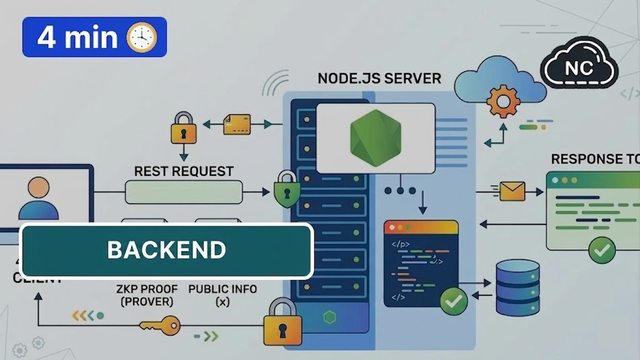
* Innowacje bliżej nas: Rozkładam na czynniki pierwsze Europejski Portfel Tożsamości Cyfrowej i kryptograficzne dowody wiedzy zerowej (Zero-Knowledge Proof), największy na kontynencie wanadowy magazyn energii w okolicach Manchesteru oraz medyczny przełom w badaniach nad niehormonalną antykoncepcją dla mężczyzn (białko ARRDC4).
Gdzie leży granica między automatyzacją a intelektualną kapitulacją? Zapraszam do słuchania i dyskusji!
https://wtfs.stream/@what_the_fox_says/episodes/odcinek-kosmiczny
#WhatTheFoxSays #Astrofizyka #NASA #BlueOrigin #Starlink #Razvet #MistralAI #AI #Deskilling #Kryptografia #ZKP #Vanadium #ARRDC4 #Nauka #Technologia

Odcinek kosmiczny
W tym odcinku: (00:25) Przywitanie (00:37) Teleskop Webba odkrywa niezwykłe planety (04:06) Jak powstają czarne dziury (07:31) Kosmiczne silniki i lądowniki przyszłości (12:34) Rosyjska odpowiedź na Starlink (18:48) Europejska odpowiedź na SpaceX (22:53) Krytyczny moment dla Europy (26:46) Ludzie tracą umiejętności (32:31) Europejski Portfel Tożsamości Cyfrowej (36:13) Brytyjska infrastruktura inteligentnego węzła energetycznego (39:43) Przełom w męskiej antykoncepcji (43:33) Pożegnanie ===== Zapraszam do komentowania pod odcinkiem na stronie https://wtfs.stream/@what_the_fox_says Podoba Ci sie mój podcast? Możesz wspomóc podcast na https://ko-fi.com/whatthefoxsays Mój mastodon: https://social.lol/@fox Mój Signal: @foxerek.01 Mój Telegram: @foxerek ===== Link partnerski do mydevil - niezawodne serwery WWW z intuicyjnym, autorskim panelem zarządzania, który łączy łatwość obsługi z najwyższą wydajnością. Użytkownicy poleceni przez mnie zyskują 20% zniżki na pierwszą wpłatę. Program działa dla każdej usługi (poza doładowaniem wirtualnego portfela) http://www.mydevil.net/pp/whatthefoxsays ===== Źródła: Teleskop Webba odkrywa niezwykłe planety https://scitechdaily.com/webb-space-telescope-reveals-rare-planet-pair-that-shouldnt-exist/ Jak powstają czarne dziury https://scitechdaily.com/scientists-just-discovered-how-the-universe-builds-monster-black-holes/ Kosmiczne silniki i lądowniki przyszłości https://scitechdaily.com/nasa-fires-up-record-breaking-plasma-thruster-for-future-mars-missions/ https://scitechdaily.com/blue-origins-new-moon-lander-passes-a-crucial-test-for-nasa-missions/ Rosyjska odpowiedź na Starlink https://www.wired.com/story/meet-rassvet-russias-answer-to-starlink/ Europejska odpowiedź na SpaceX https://scitechdaily.com/europe-just-unveiled-a-serious-rival-to-spacexs-starship/ Krytyczny moment dla Europy https://www.businessinsider.com/mistral-ceo-warns-europe-2-years-avoid-us-ai-dependence-2026-5 Ludzie tracą umiejętności htttps://news.harvard.edu/gazette/story/2026/05/deskilling-is-bad-this-is-worse/ Europejski Portfel Tożsamości Cyfrowej https://www.wirtualnemedia.pl/weryfikacja-wieku-w-sieci-rzad-przedstawil-mechanizm-oparty-na-europejskim-portfelu-tozsamosci-cyfrowej,7285855486269504a Brytyjska infrastruktura inteligentnego węzła energetycznego https://electrek.co/2026/05/11/uk-delivers-europes-largest-vanadium-flow-battery-system/ Przełom w męskiej antykoncepcji https://scitechdaily.com/male-birth-control-breakthrough-scientists-find-way-to-turn-sperm-production-off-and-back-on/ =====