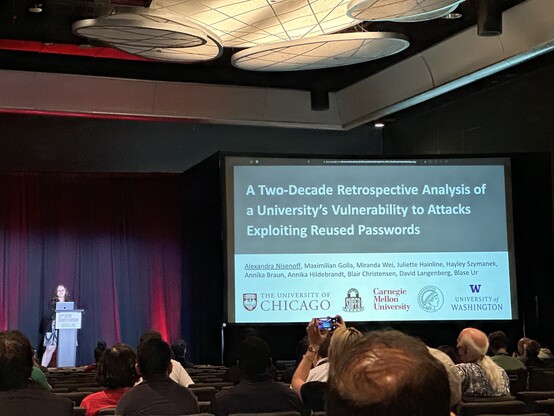
" @DianaInitiative, @BSidesLV, #BHUSA, #SquadCon, #usesec23 @usenixassociation , @defcon...#hackersummercamp is now truly over!"
Hobbit Voice: Yeah but what about 2nd Hacker Summer Camp?
@CCC #cccamp23, #wikimania '23 & #hackconXI by #MLH begin this week!
#DCG201 Guides: https://defcon201.medium.com