🎉 @acm_ccs 2025 in Taipei, Taiwan was a blast!
I had a great time connecting with colleagues and friends at ACM SIGSAC's flagship security conference — a week filled with inspiring research and thoughtful discussions.
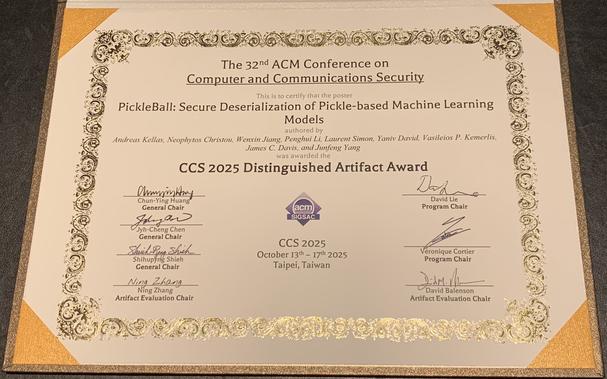
I was also deeply honored to receive two awards this year (https://www.sigsac.org/ccs/CCS2025/awards/):
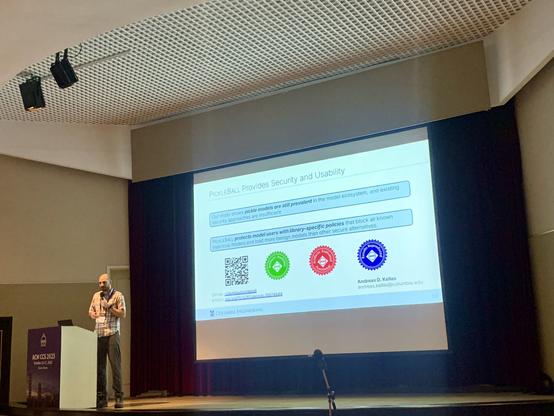
🏅 Distinguished Artifact Award for our paper "PickleBall: Secure Deserialization of Pickle-based Machine Learning Models" (https://infosec.exchange/@vkemerlis/115409982332037503).
🏆 Top Reviewers Award, recognizing service and contributions to the CCS community. I'm especially grateful for this honor, as it marks the third consecutive year (2023, 2024, and 2025) that I've received a service award from CCS — a tradition I'm proud to continue.
Contributing to the community—through both research and reviewing—has been one of the most fulfilling aspects of my academic career. Many thanks to the organizers, colleagues, and students who make CCS such a vibrant and rigorous forum for computer security research!