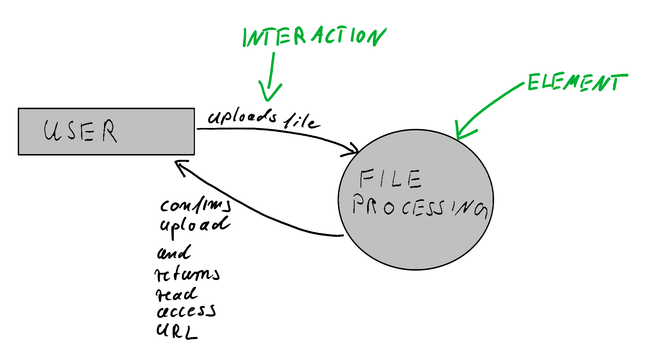
I had to structure my knowledge and my thoughts. So I did write an article on Threat Modeling.
Maybe you find that helpful.
https://blog.maschmi.net/threat-modeling
If you attend the SoCraTes Day Franken tomorrow, you might have the experience of me giving a non-rehearsed talk about this. (Depending on my energy levels). Might be 30 to 120 minutes long 😅