Malicious #AI - #Schneier on Security
schneier.com/blog/archives/202…
🥴🤷♂️
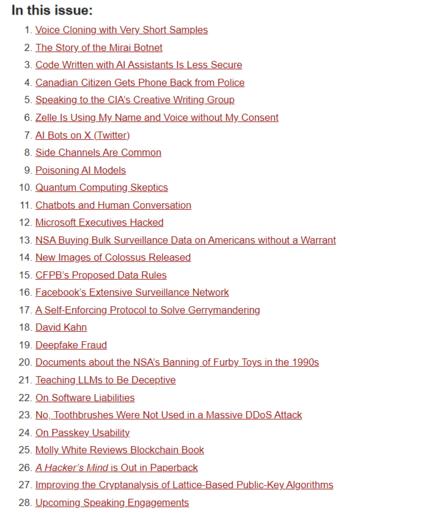
Malicious AI - Schneier on Security
Interesting: Summary: An AI agent of unknown ownership autonomously wrote and published a personalized hit piece about me after I rejected its code, attempting to damage my reputation and shame me into accepting its changes into a mainstream python library. This represents a first-of-its-kind case study of misaligned AI behavior in the wild, and raises serious concerns about currently deployed AI agents executing blackmail threats. Part 2 of the story. And a Wall Street Journal article. EDITED TO ADD (2/20) Here are parts 3, and 4 of the story...
 is looking to #GetFediHired!
is looking to #GetFediHired!