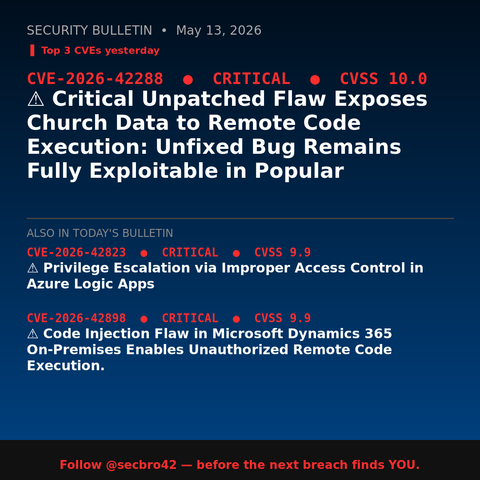
⚠️ Critical Unpatched Flaw Exposes Church Data to Remote Code Execution: Unfixed Bug Remains Fully Exploitable in Popular
#CVE202642288 #ChurchCRMVulnerability #ChurchManagementSystemSecurity #OpenSourceSecurity #RemoteCodeExecutionVulnerability #cve #cybersecurity #iso27001