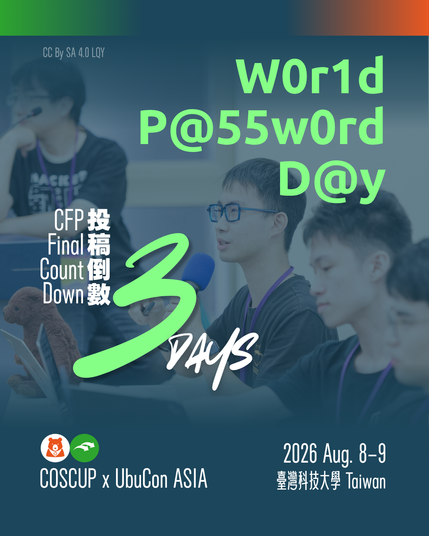
🔐 COSCUP x UbuCon Asia 2026 CFP closes in 3 days — and today happens to be World Password Day.
📅 CFP Deadline: 2026/5/9 AoE
📨 Submit your proposal: https://pretalx.coscup.org/coscup-2026/cfp
📖 CFP announcement: https://blog.coscup.org/2026/03/coscup-x-ubucon-asia-2026-coscup-x.html
#COSCUP2026 #UbuConAsia #HITCON #CyberResilience #CyberSecurity #OpenSource #OpenSourceSecurity