https://interlaye.red/kubernetes_002degress_002dsquid.html #Egress #RetroTech #CloudComputing #HackerNews #ngated
https://interlaye.red/kubernetes_002degress_002dsquid.html #Egress #RetroTech #CloudComputing #HackerNews #ngated
Công cụ Python mới giúp đánh giá nhanh bảo mật Kubernetes NetworkPolicy đã ra mắt! Nó cung cấp điểm số trực quan cho namespace, workload và cảnh báo về các chính sách không an toàn. Đây là bản MVP, tác giả rất mong nhận được phản hồi để cải thiện.
#Kubernetes #NetworkPolicy #Security #Python #Tool #BảoMật #CôngCụ
https://www.reddit.com/r/SideProject/comments/1orlpsg/i_built_a_python_tool_to_quickly_evaluate/
Mình 개발 công cụ Python đánh giá an ninh Kubernetes NetworkPolicy nhanh. Cung cấp điểm tư duy và gợi ý chính sách không an toàn. MVP────—ocket cùng mình partager! facebook.com/SaSa0011/policyshield #Kubernetes #NetworkPolicy #PythonTool #CôngTừPython #CyberSecurity
https://www.reddit.com/r/SaaS/comments/1orlnd8/i_built_a_python_tool_to_quickly_evaluate/
#Drupal #Kubernetes #Terraform #Infrastructure #Automation #IaC #DevOps #CloudNative #Microservices #Networkpolicy #PaaS #SaaS #IaaS #Helm #OpenSource
Want to Run Drupal in Kubernetes? Try Our New Terraform Module
Background Our customer dashboard, which will soon be used for managing subscriptions to our backup service (and not just newsletters and our contact form, as we’re doing now), is built on the Drupal data management framework. Until now, we’ve been hosting it with a company that specializes in hosting very specific types of applications, like Drupal. This wasn’t working for us because our service is running in our Kubernetes cluster at a cloud service provider that specializes in managed Kubernetes hosting, which let’s us run whatever applications we want, and configure them however we need.
Безопасность Kubernetes-кластеров: вредные советы или bullshit bingo
Как погубить кластер, действуя во благо? Подборка вредных советов из реальных кейсов и опыта от специалиста по безопасности контейнеров и Kubernetes. Вместе установим антивирус на ноды, просканируем хостовую ОС и заблокируем выкатки образов с чувствительной информацией. Привет, Хабр! Меня зовут Дмитрий Евдокимов. Я — Founder & CTO Luntry в компании по созданию решений для безопасности контейнеров и Kubernetes, CFP конференций DevOpsConf и Highload, автор курса «Cloud-Native безопасность в Kubernetes» и телеграм-канала k8s (in) security. Эта статья написана по мотивам моего доклада для DevOpsConf 2024. Так как я проработал в сфере информационной безопасности больше 15 лет и специализируюсь именно на безопасности контейнеров и кластеров, дам несколько «вредных» советов, как сделать Kubernetes-кластер «безопасным». Погубить кластер
https://habr.com/ru/companies/oleg-bunin/articles/875114/
#кубернетес #контейнеры #оркестрация_микросервисов #окружение #shift_left_security #уязвимости #distroless #zerotrust #NetworkPolicy #apparmor
An interesting article on #kubernetes networking
https://otterize.com/blog/mastering-kubernetes-networking-otterize-s-journey-in-cloud-native-packet-management
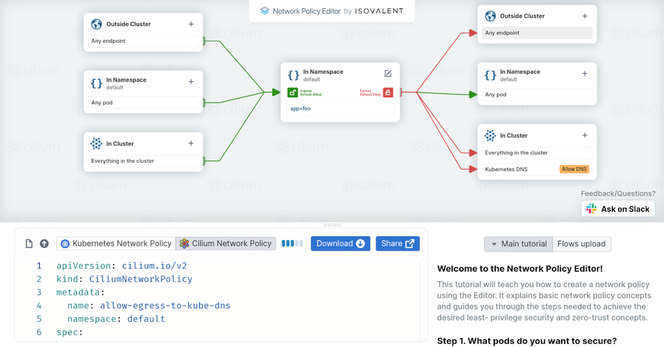
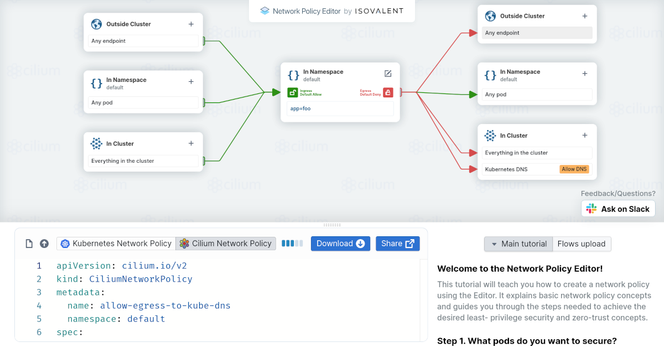
Network policies can be difficult to grasp, but this video provides the clarity you need to understand network policy concepts through hands-on examples. Additionally, I demonstrate how you can create a Cilium-based network policy for Layer 7 HTTP, a capability not achievable with standard Kubernetes network policy.
How do you restrict the traffic within your cluster Let me know in the comments.👇
#kubernetes #networkpolicy #cilium
https://youtu.be/Fr-6oDHbobM?si=DyxG4N6i-fP7EVxP
Kubernetes Network Policy Deep Dive
Ever fought to write a Kubernetes network policy? Well, while it may be hard to write straight to YAML, here is a graphical tool that writes YAML for you.
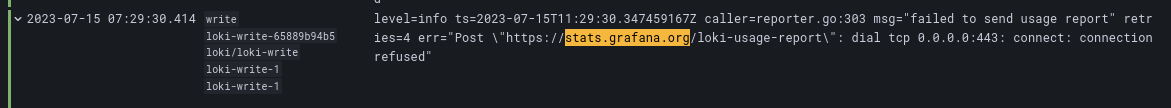
Today's adventure in #darkpattern #surveillance comes from #Grafana #Loki. (Not a surprise, but this is why I run egress filters and dns #adblock in my #homelab clusters.)
I know not everyone agrees that #optout #telemetry is a dark pattern, but you might agree with me about this one after you see it documented:
> # -- Optional analytics configuration
> analytics: {}
Enlightening, isn't it? There are other empty blocks, but they are either fairly standard or are described elsewhere in the document.
If you are familiar with #helm, you won't despair because you have the power of `analytics.enabled: false`. That works on the rest of this chart and is the standard way to en/disable things.
It doesn't work that way.
Let me save you some time with the terrible new #github code search. Here is the actual syntax:
"analytics.reporting_enabled: false"
This was caught by #adguard and enforced by an egress #networkpolicy