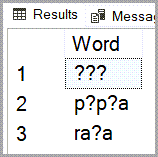
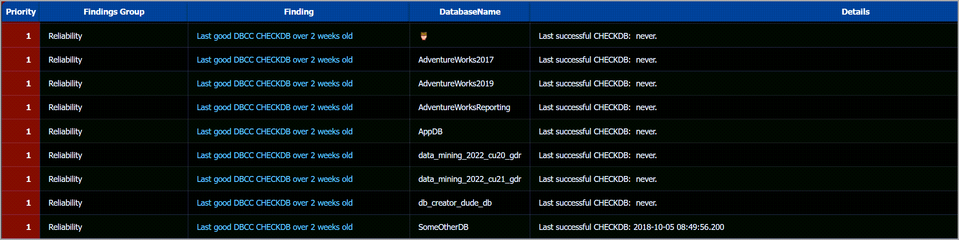
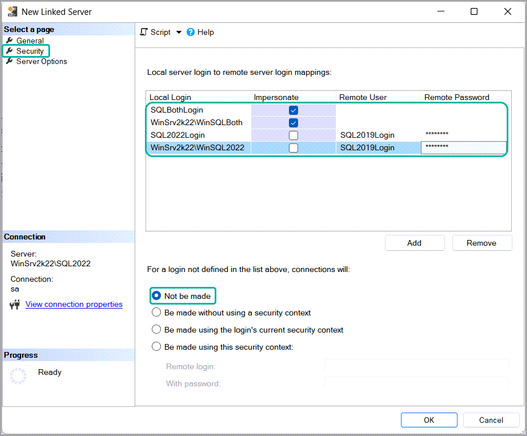
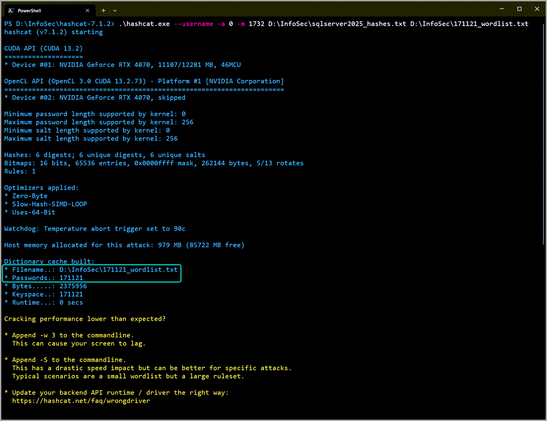
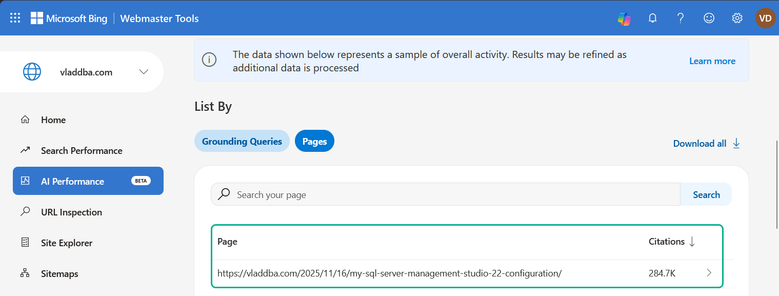
In which I go over potential reasons for why some special characters end up corrupted and displayed as question marks, squares or something completely different in SQL Server.
https://vladdba.com/2024/10/04/characters-question-marks-squares-sql-server/
#sqlserver #sqldba #microsoftsqlserver #mssqlserver #mssql #mssqldba