🔵🟡 Government Hacking Tools Are Now in Criminals' Hands (with @lorenzofb.bsky.social @lorenzofb )
by Joseph Cox @josephcox
at 404 Media
@404media.co @404mediaco
#HackingTools #Hacked #Leaked #podcast #cybersecurity
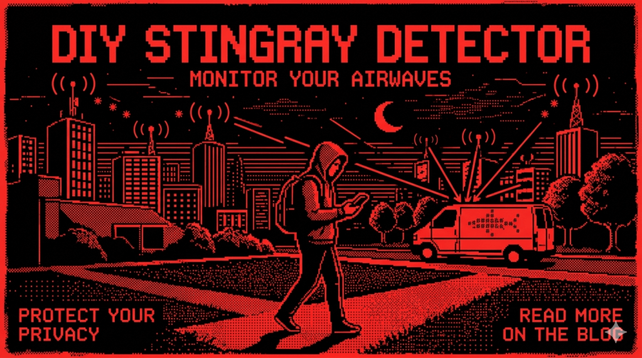
Building a $40 Stingray Detector That Fits in an Altoids Tin
You don’t see IMSI catchers. You don’t hear them. They sit between your phone and the network like a polite lie, impersonating a tower just well enough that your device shrugs and connects anyway. No warning. No vibration. Nothing in the UI suggests that your phone has just been convinced to trust something it never verified.🎖️ El Curso de Hacking Ético está permanente disponible en el aula virtual para acceso inmediato. 📲 WhatsApp: https://wa.me/51949304030 🌐 https://www.reydes.com/e/Curso_de_Hacking_Etico
#hackers #ethicalhacker #hacking #cybersecurity #cyber #kalilinux #hackingtools
Want to learn and expand your cybersecurity toolset?
Look no further than our Group!
Best pentesters ("hackers") toolkits
Telegram: https://t.me/ZannysMarket
This Is What a Personal Surveillance System Actually Looks Like
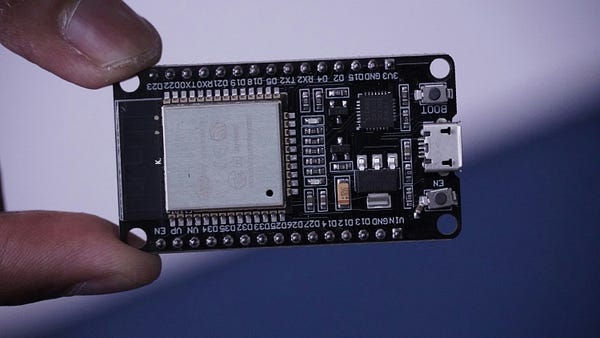
You stop thinking of it as surveillance. It becomes “the system.” Just part of how things run.What Actually Happens When You Leave an ESP32 Running 24/7
Heap fragmentation is the quiet one. It doesn’t crash immediately. It just reshapes what’s available. Allocations that worked on day one start failing in strange ways. Not clean failures either. Partial allocations. Corrupted data. Functions returning values that feel slightly off.How I Use Obsidian to Capture, Distill, and Weaponize Ideas
Ideas rarely stand alone. They’re fragments of larger structures. When you link a note to two or three others, something starts to form. Not a hierarchy. More like pressure building in certain areas of the graph.From Raw Data to Actionable Intelligence Without Leaving My System
The room is quiet except for a fan that shouldn’t be that loud. Not the kind of noise you notice at first. It creeps in. A low mechanical breath that suggests something is working harder than it should. On the desk, a phone face-down, a laptop half-closed, a terminal window still alive somewhere beneath the sleep state. Nothing dramatic. Just the kind of setup most people would call normal. It isn’t. Most people think intelligence happens after the data leaves their system. They ship […]