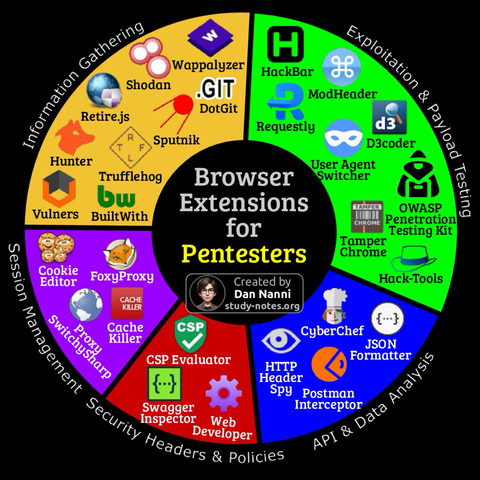
Pentesters often use browser extensions because they keep testing close to the web app—making it easier to inspect cookies, tweak traffic, and catch client-side issues without constantly switching tools
Here are useful browser extensions for pentesting 😎👇
Find high-res pdf ebooks with all my cybersecurity related infographics at https://study-notes.org
#pentesting #cybersecurity #hackingtools #learnhacking #ethicalhacker