Alright team, it's been a pretty packed 24 hours in the cyber world! We've got some significant breaches to cover, a raft of actively exploited vulnerabilities, and a deep dive into how threat actors are increasingly leveraging AI for everything from malware generation to sophisticated social engineering. Let's get stuck in:
Recent Cyber Attacks and Breaches 🚨
- The FBI is investigating a breach of its systems used to manage surveillance and wiretap warrants, though details on scope and impact are limited. This follows previous incidents, including a 2024 compromise by Chinese Salt Typhoon hackers targeting US government wiretapping platforms via telecom networks.
- Transport for London (TfL) has confirmed that a 2024 breach exposed data for over 7 million customers, a significant increase from the initially reported 5,000. While only 5,000 had bank account data potentially accessed, the larger figure represents the total dataset sitting in the compromised systems.
- The son of a US government contractor has been arrested in the Caribbean, accused of stealing over $46 million in seized cryptocurrency from the US Marshals Service. The alleged theft, traced by blockchain investigators, involved funds from previous seizures, including a portion linked to the 2016 Bitfinex hack.
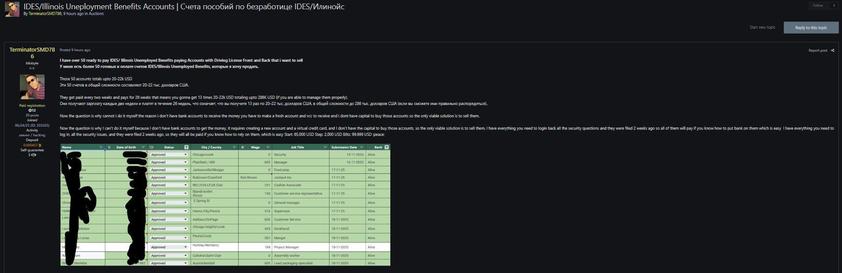
- A small group of hacktivists compromised at least nine Mexican government agencies, stealing over 195 million identities and tax records, plus other sensitive data. The attackers notably used Anthropic's Claude and OpenAI's ChatGPT, bypassing their guardrails within 40 minutes to find vulnerabilities and build attack tools.
🤖 Bleeping Computer | https://www.bleepingcomputer.com/news/security/fbi-investigates-breach-of-surveillance-and-wiretap-systems/
🕵🏼 The Register | https://go.theregister.com/feed/www.theregister.com/2026/03/06/tfl_2024_breach_numbers/
🕵🏼 The Register | https://go.theregister.com/feed/www.theregister.com/2026/03/06/contractor_son_crypto_arrest/
🕶️ Dark Reading | https://www.darkreading.com/application-security/cyberattack-mexico-government-ai-threat
Actively Exploited Vulnerabilities and Zero-Days 🛡️
- Google's Threat Intelligence Group reported 90 actively exploited zero-days in 2025, with enterprise tech products seeing an all-time high of 43. China-linked cyber-espionage groups were the most prolific state-backed actors, particularly targeting security and networking edge devices.
- CISA has ordered federal agencies to patch three iOS security flaws (CVE-2023-41974, CVE-2021-30952, CVE-2023-43000) actively exploited by the Coruna exploit kit. Coruna, a sophisticated spyware-grade kit, has been used by surveillance vendors, suspected Russian state-backed groups, and financially motivated Chinese actors for cyberespionage and crypto-theft.
- Two critical-severity flaws, CVE-2017-7921 (Hikvision) and CVE-2021-22681 (Rockwell Automation), with CVSS scores of 9.8, have been added to CISA's KEV catalog due to active exploitation. Federal agencies must patch these by March 26, 2026, with all organisations strongly urged to do the same.
- Cisco has warned of two more actively exploited vulnerabilities in its Catalyst SD-WAN Manager: CVE-2026-20122 (CVSS 7.1) allowing arbitrary file overwrites, and CVE-2026-20128 (CVSS 5.5) for information disclosure. This follows a recent Five Eyes alert about other SD-WAN flaws, highlighting persistent targeting of these critical network devices.
🕵🏼 The Register | https://go.theregister.com/feed/www.theregister.com/2026/03/05/zero_day_attacks_enterprise_tech_record/
🤖 Bleeping Computer | https://www.bleepingcomputer.com/news/security/cisa-warns-of-apple-flaws-exploited-in-spyware-crypto-theft-attacks/
📰 The Hacker News | https://thehackernews.com/2026/03/hikvision-and-rockwell-automation-cvss.html
🕵🏼 The Register | https://go.theregister.com/feed/www.theregister.com/2026/03/06/cisco_sdwan_bugs/
New Threat Research and Tradecraft 🕵️♀️
- Europol, alongside Microsoft, Trend Micro, and Cloudflare, has disrupted Tycoon 2FA, a major phishing-as-a-service (PhaaS) platform. Tycoon 2FA was notorious for its adversary-in-the-middle (AitM) attacks that bypassed traditional MFA by relaying authentication prompts in real-time to steal session tokens.
- Microsoft has detailed a new ClickFix social engineering campaign that leverages the Windows Terminal app to deploy the Lumma Stealer malware. Attackers instruct users to launch Windows Terminal and paste hex-encoded, XOR-compressed commands, bypassing traditional Run dialog detections and blending into legitimate administrative workflows.
- A new InstallFix technique, a variation of ClickFix, is being used to push info-stealing malware like Amatera via fake CLI tool installation guides. Threat actors promote these cloned pages, often hosted on legitimate platforms like Squarespace, through malvertising on Google Ads, tricking users into executing malicious `curl-to-bash` commands.
- Bing AI's search feature was observed promoting fake OpenClaw GitHub repositories that pushed information-stealing and proxy malware. Threat actors created seemingly legitimate GitHub organisations and repositories, which were then recommended by Bing AI, leading users to install Atomic Stealer or Vidar stealer and GhostSocks proxy malware.
- A China-linked APT, UAT-9244 (associated with FamousSparrow and Tropic Trooper), is targeting South American telecom providers with a new malware toolkit. This includes TernDoor (Windows backdoor), PeerTime (Linux backdoor using BitTorrent for C2), and BruteEntry (a brute-force scanner building proxy infrastructure).
- The Pakistan-aligned Transparent Tribe APT is using AI-powered coding tools to mass-produce "vibeware" malware implants in a campaign targeting India. This "Distributed Denial of Detection" (DDoD) strategy involves flooding targets with high-volume, mediocre binaries written in lesser-known languages like Nim, Zig, and Crystal, relying on trusted services for C2.
- North Korean APTs Jasper Sleet and Coral Sleet are enhancing their IT worker scams with AI to improve scale and precision. AI assists in fabricating convincing digital identities, generating resumes and cover letters, maintaining personas during interviews (including voice-changing software), and even developing malware and automating attack workflows.
- Iran has reportedly unified cyber and kinetic attacks into a single doctrine, leveraging IP camera compromises for operational support and battle damage assessment during missile strikes. Check Point Research observed intensified targeting of Hikvision and Dahua cameras in the Middle East, with activity patterns correlating with kinetic events.
🕶️ Dark Reading | https://www.darkreading.com/threat-intelligence/tycoon-2fa-europol-vendors-bust-phishing-platform
📰 The Hacker News | https://thehackernews.com/2026/03/microsoft-reveals-clickfix-campaign.html
🕵🏼 The Register | https://go.theregister.com/feed/www.theregister.com/2026/03/06/microsoft_spots_clickfix_campaign_abusing/
🤖 Bleeping Computer | https://www.bleepingcomputer.com/news/security/fake-claude-code-install-guides-push-infostealers-in-installfix-attacks/
🤖 Bleeping Computer | https://www.bleepingcomputer.com/news/security/bing-ai-promoted-fake-openclaw-github-repo-pushing-info-stealing-malware/
🤖 Bleeping Computer | https://www.bleepingcomputer.com/news/security/chinese-state-hackers-target-telcos-with-new-malware-toolkit/
📰 The Hacker News | https://thehackernews.com/2026/03/transparent-tribe-uses-ai-to-mass.html
🕶️ Dark Reading | https://www.darkreading.com/threat-intelligence/north-korean-apts-ai-it-worker-scams
🕶️ Dark Reading | https://www.darkreading.com/threat-intelligence/iran-cyber-kinetic-war-doctrine
Regulatory Issues and Data Privacy ⚖️
- The House Energy and Commerce Committee advanced the Kids Internet and Digital Safety (KIDS) Act in a party-line vote, drawing criticism from Democrats for perceived weak regulations. Concerns include a "toothless" knowledge standard for tech companies, lack of a "duty of care" to proactively mitigate harms, and preemption language that could undercut stronger state laws.
- Other bills marked up include Sammy's Law, aiming to notify parents of child risk on third-party safety apps, and the App Store Accountability Act, requiring parental consent for app downloads by minors. Digital freedom advocates criticised these bills for potentially threatening privacy and free expression by pushing age assurance techniques.
🗞️ The Record | https://therecord.media/house-panel-marks-up-kids-digital-safety-act
Government Staffing and Program Changes 🏛️
- The Department of Homeland Security (DHS) is undergoing a significant IT and information security leadership overhaul, with CISO Hemant Baidwan and Deputy CISO Amanda Day reportedly being replaced. This realignment, led by DHS CIO Antoine McCord, aims to centralise IT control and follows other high-profile departures at CISA and FEMA.
- Congress is moving to reauthorise and fund the Rural and Municipal Utility Advanced Cybersecurity program at the Department of Energy, approving $250 million in grants over five years. This program is crucial for smaller utilities, often lacking robust cybersecurity operations, to defend against escalating threats, including those from nation-state actors like Volt Typhoon.
🤫 CyberScoop | https://fedscoop.com/dhs-it-leadership-overhaul-includes-ciso-deputy-ciso/
🤫 CyberScoop | https://cyberscoop.com/house-committee-advances-rural-utility-cybersecurity-act/
Cybercrime and Law Enforcement 💰
- A Ghanaian national, Derrick Van Yeboah, has pleaded guilty to his role in a $100 million fraud ring involving business email compromise (BEC) attacks and romance scams. Yeboah, a high-ranking member of the Ghana-based operation, personally conducted many romance scams, contributing to over $10 million in losses.
- The scammers targeted vulnerable individuals online, tricking them into depositing money into US middlemen's accounts, and also defrauded businesses via spoofed emails. Yeboah faces up to 20 years in prison and has agreed to pay over $10 million in restitution.
🤖 Bleeping Computer | https://www.bleepingcomputer.com/news/security/ghanain-man-pleads-guilty-to-role-in-100-million-fraud-ring/
#CyberSecurity #ThreatIntelligence #InfoSec #CyberAttack #ZeroDay #Vulnerability #APT #Malware #Phishing #AI #SocialEngineering #DataPrivacy #GovernmentSecurity #LawEnforcement #IncidentResponse