https://arxiv.org/abs/2512.05358
#BGP #FuzzTesting
BGPFuzz: Automated Configuration Fuzzing of the Border Gateway Protocol
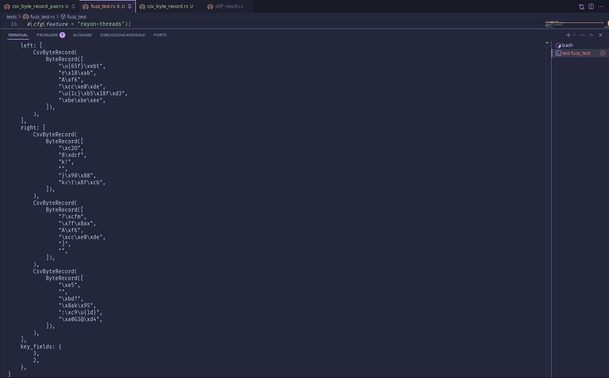
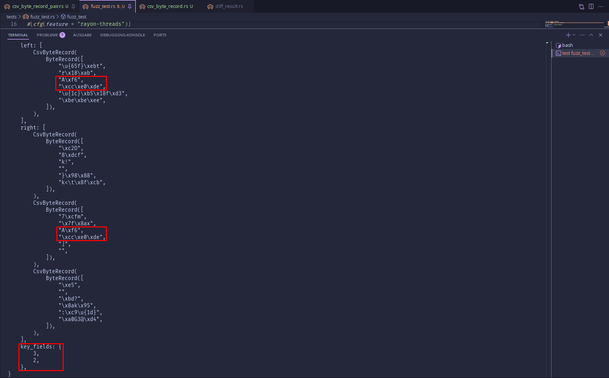
Telecommunications networks rely on configurations to define routing behavior, especially in the Border Gateway Protocol (BGP), where misconfigurations can lead to severe outages and security breaches, as demonstrated by the 2021 Facebook outage. Unlike existing approaches that rely on synthesis or verification, our work offers a cost-effective method for identifying misconfigurations resulting from BGP's inherent complexity or vendor-specific implementations. We present BGPFuzz, a structure-aware and stateful fuzzing framework that systematically mutates BGP configurations and evaluates their effects in virtualized network. Without requiring predefined correctness properties as in static analysis, BGPFuzz detects anomalies through runtime oracles that capture practical symptoms such as session resets, blackholing, and traffic redirection. Our experiments show that BGPFuzz can reliably reproduce and detect known failures, including max-prefix violations and sub-prefix hijacks.