Challenge 50 goes by the wayside.
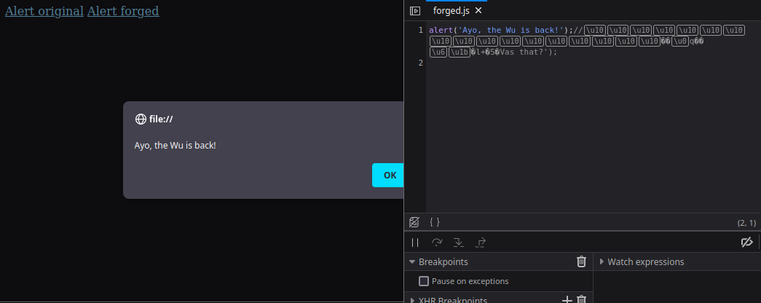
The opposite of the last challenge, this time prepending (forged javascript) with the aim to make the same cbc mac.
As for the last challenge xor'ing the mac of the first part (our forged javascript) with the first block of the 2nd part (the javascript we wish to 'replace') results in the same cbc mac for the whole javascript snippet, which still runs in a browser.
There are probably other ways but this was easy to implement.