Customer: "We'd like to save some money on licensing costs and switch from #RHEL to #AL2023"
Me: "Cool. Lemme check some things…"
Me: (Looks at Compliance as Code project) "Looks like Amazon isn't participating in that project, so, all our ready-to-go automation that leverages that won't work. Don't worry, it's not necessarily fatal, their distro has oscap content, so, I'll check that…"
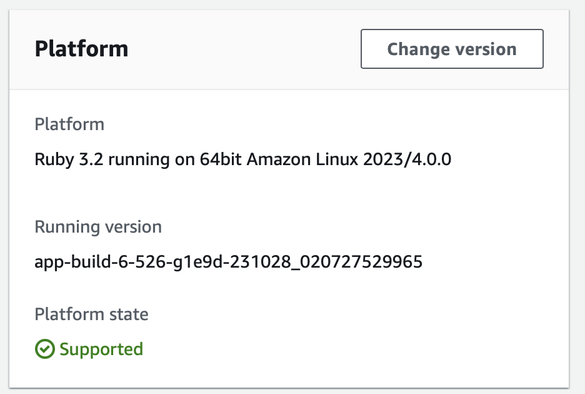
Me: (fires up and al2023 #EC2 and sees what Amazon makes available) "Looks like Amazon only makes available one hardening profile:
Title: Standard System Security Profile for Amazon Linux 2023I have no freaking clue what that maps to, as far as common frameworks. Normally, for your needs, I'd recommend STIG or CIS, possibly even PCI/DSS or HIPAA. However, neither Amazon's tooling nor the Compliance as Code project seems to have those for AL2023. By point of comparison, I've checked not just the RHEL distro — that you wanted to avoid licensing costs on — but all the license-cost free ones that I know of — Oracle Enterprise Linus, CentOS Stream, Alma Linux and Rocky Linux and they all support STIG, CIS, PCI/DSS, HIPAA and others (all the same "others" that Red Hat does). I can't promise you that your accreditors are going to accept whatever the hell Amazon's "standard" hardening is, nor can I guarantee that your third-party scanning tools are going to be happy. All I can sorta guarantee is that if you use _Amazon's_ tools to verify _Amazon's_ profiles, that you'll probably get all greens if you stay up to date on patches. But you've also told me that you want to be multi-cloud by the end of next year: even ignoring your auditors and your thirde-party scanning tools, I'm not sure how helpful that's going to be to you.

 have been writing up my notes into a new blog post. HURRAH!
have been writing up my notes into a new blog post. HURRAH!