RBAC defeats: A compromised pod, a stolen kubeconfig, a rogue user — anyone who tries to read secrets through the Kubernetes API without sufficient permissions. They hit the apiserver, RBAC says no, they get a 403.
secretbox defeats: Someone who bypasses the API entirely — steals the etcd data directory, takes an etcd snapshot from a backup, reads etcd directly over its client port without going through kube-apiserver. RBAC never runs in this scenario because the attacker never talked to kube-apiserver.
The critical insight: secretbox does nothing if the attacker has API access, and RBAC does nothing if the attacker has disk access. They cover completely non-overlapping attack surfaces.
problem hit here would have been identical with #SQLite — the encryption layer is in kube-apiserver, not in the storage backend. But the operational simplicity of SQLite would have made recovery easier since inspecting and backing up the database is much more straightforward than #etcd snapshot management.
#kubernetes
Weil es letztes Jahr beim #Tübix2025 so gut angekommen war, mache ich wohl beim #Tübix2026 sogar zwei  #NixOS workshops:
#NixOS workshops:
1. Workshop: Einstieg, Motivation, Killer Features, Basics
2. Workshop: Deep Dive ins Nixos-Modulsystem, schreiben eigener Module, secrets management mit #agenix, vllt. Live-Deployment auf einen  #RaspberryPi vor Ort
#RaspberryPi vor Ort
Was meint ihr?
Why?
#nix is it some race condition analogous async callback which don't go well for pure Haskell without alib
very cool
Secret provisioning in #nix
Many options in nix for authentication only accept files and not string
Whereas #Unix #pass show just give a string , even if you store it in some file it ll be mutable and not reproducible, hence I end up with #age #agenix #sops
and none of them re interoperable with pass which is my daily driver
So I need store them somewhere safe on #vps or #cloud or idk mod/wrap these these things for interoperability *, or seek some #nocloud solution.
What's the simplest option me ?
* Its more work then reward , since I am not an active community contributor, just a user ,
#it folks ?
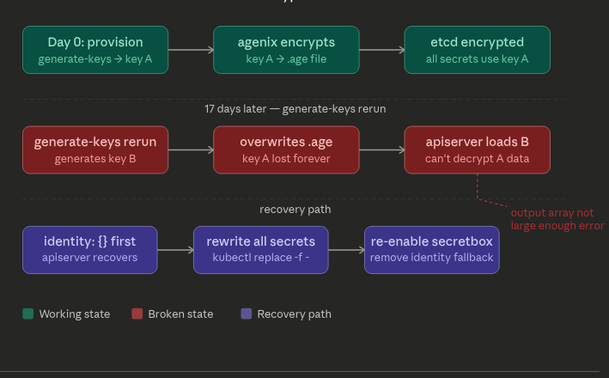
https://www.splitbrain.org/blog/2025-07/27-agenix
#blogpost
How are people who use #agenix solving passing secrets to modules that don't take a path? I'm specifically looking at my Prometheus config where I need to configure a bearer token for a scrape job, and API tokens in the Alertmanager configuration. All of these just take strings.
I guess you can lib.readFile the decrypted file which is frowned upon, but there's no other users on the system so I guess having it in the clear in the store is less of an issue.
For the former , I end up needing impure as I fetch my authorizedsshkeys from github , among other things
Despite #agenix