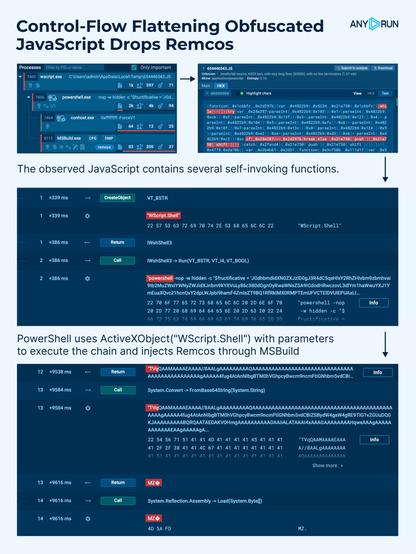
🚨 Control-Flow Flattening Obfuscated #JavaScript Drops #Remcos.
⚠️ The observed JS contains multiple self-invoking functions that loop arrays of strings and numbers in a while(!![]) loop until a calculated checksum matches a predefined value. This #obfuscation technique forces static analyzers to parse through the array content instead of returning the required string directly.
🎯 #ANYRUN’s Script Tracer enables easy analysis of heavily obfuscated scripts by logging their execution in real time, with no need for manual deobfuscation.
🔗 Execution chain:
#Wscript (JavaScript) ➡️ PowerShell ➡️ MSBuild (Remcos 🚨)
👨💻 See analysis session: https://app.any.run/tasks/eaef10ea-3567-4284-b87e-a3a0aedc5f83/?utm_source=mastodon&utm_medium=post&utm_campaign=obfuscated_js_drops_remcos&utm_term=110625&utm_content=linktoservice
This script invokes #PowerShell using ActiveXObject("http://WScript.Shell") with parameters and executes the following:
🔹 Creates a http://System.Net.WebClient object
🔹 Specifies the URL to download the binary
🔹 Downloads the binary data and passes it to #MSBuild
⚠️ As a result, the script downloads and executes the Remcos #malware module.
👨💻 Observe obfuscated loaders, explore execution flows, and extract behavioral indicators in real time. Improve your security operations with #ANYRUN Sandbox.
 Hacker News
Hacker News