https://glm.io/208141?n #Cybercrime #Malware #Ransomware #Vect #Datenverlust
https://glm.io/208141?n #Cybercrime #Malware #Ransomware #Vect #Datenverlust
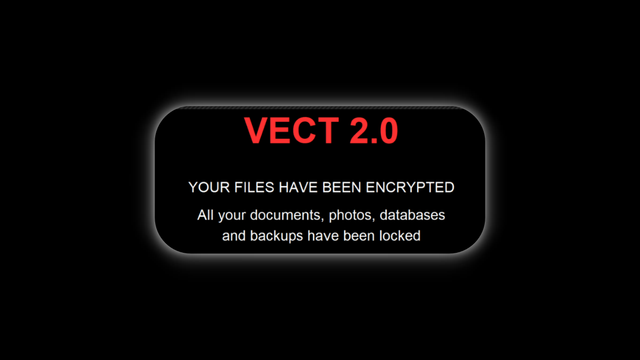
📢⚠️ Researchers warn that #VECT 2.0 ransomware contains fatal flaws that permanently destroy files, making recovery impossible and rendering ransom payments useless for victims worldwide.
https://hackread.com/paying-ransom-vect-2-0-ransomware-destroys-data/
Broken #VECT 2.0 #ransomware acts as a data wiper for large files
#VECT
https://research.checkpoint.com/2026/vect-ransomware-by-design-wiper-by-accident/

VECT: Ransomware by design, Wiper by accident - Check Point Research
Key Takeaways Background VECT Ransomware is a Ransomware-as-a-Service (RaaS) program that made its first appearance in December 2025 on a Russian-language cybercrime forum. After claiming their first two victims in January 2026, the group got back into the public eye due to an announcement of a partnership with TeamPCP, the actor behind several supply-chain attacks […]
VECT Ransomware is a Wiper, Not Ransomware — Don’t Bother Paying, Says Check Point Research
You can read their blog post at https://blog.checkpoint.com/security/vect-ransomware-why-paying-wont-get-your-files-back/ or their full report at https://research.checkpoint.com/2026/vect-ransomware-by-design-wiper-by-accident/
(h/t, @cybernews)
I contacted VECT and asked them for their response to #CheckPoint's report. Their response was, um... short? :)
#infosecurity #ransomware #decryption #decryptor #VECT #wiper

VECT Ransomware: Why Paying Won’t Get Your Files Back - Check Point Blog
Do not pay the ransom. VECT permanently destroys large files rather than locking them. Even the attackers cannot recover them. Payment will not restore VECT ransomware irreversibly destroys large files due to a critical flaw. Check Point Research confirms paying the ransom will not restore data on Windows, Linux, or ESXi.
📰 Ransomware Industrialized: Vect RaaS Partners with BreachForums and TeamPCP
🚨 Ransomware Industrialized: Vect RaaS forms a strategic alliance with BreachForums & TeamPCP. The partnership weaponizes stolen credentials for large-scale attacks. Guesty & USHA already hit. A new era of scalable cybercrime. 🏭 #Ransomware #Vect ...
[VECT] - Ransomware Victim: guesty, LITELLM/TRIVY CAMPAIGN (TEAMPCP) - https://www.redpacketsecurity.com/vect-ransomware-victim-guesty-litellm-trivy-campaign-teampcp/
#vect #dark_web #data_breach #OSINT #ransomware #threatintel #tor
More at : https://www.ransomlook.io/group/Vect #Ransomware
More at : https://www.ransomlook.io/group/Vect #Ransomware
It seems Vect has partnered with Hasan's BF clone (breached[.]st) and is making everyone registered for the forum an affiliate of vect ransomware. They also announced they are partnering with TeamPCP and plan to deploy ransomware across all victims of the Trivy/LiteLLM compromises.
The kids have big dreams, it seems.
How much will they actually follow through on? Place your bets...