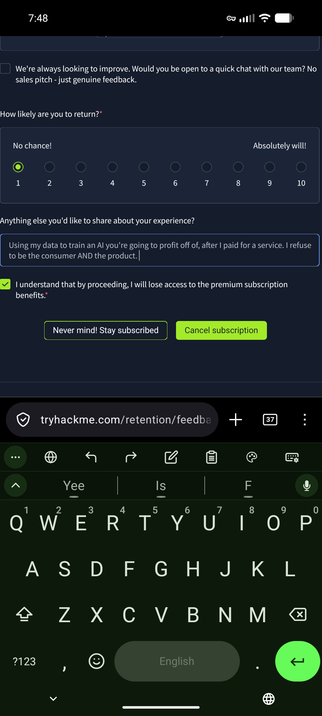
TryHackMe took my work. Work I paid a subscription to do, and fed it to NoScope, an AI they're going to profit off of. Don't teach people about security if you can't respect theirs.
#TryHackMe #NoScope #InfoSec #CyberSecurity #DataPrivacy #AIethics #EthicalHacking #HackTheBox #Privacy #ConsentMatters #DeleteYourData
I just popped a SYSTEM shell on a Windows 7 machine using my own penetration testing framework written entirely in Rust.
Amatsumara is a full exploitation framework including dynamic module loading via C FFI, interactive console, session management, 154 exploit modules, all built in Rust. Tonight I finished implementing EternalBlue (MS17-010) from scratch. Heap grooming, the SrvOs2FeaListToNt integer overflow, kernel shellcode, SrvNet buffer corruption, OS detection to automatically route between Win7 and Win8 exploit paths.
Now I have to try to find a way to sleep and not keep messing around in excitement.
#Rust #RustLang #Infosec #Cybersecurity #PenTesting #EternalBlue #MS17010 #ExploitDevelopment #CTF #TryHackMe #RedTeam #Hacking #OpenSource
SEC0 from @RealTryHackMe done.
I know it’s a fundamental's certification, but I treated it like it wasn’t. Went back over weak areas. I completed the exam.
Next step: SEC1.
Hello, again 
Today is officially the worst day of this month, no electricity whole day, I wasn't able to get much done, I did do a little bit of packet analysis.
I can confidently identify common nmap scans. It all boils down to the TCP three way handshake for the TCP connect scan, and Stealth scan.
UDP scan utilizes the icmp protocol to scan the open ports.
Hello, again 
Today is a special day because two great things happened to me. First, I reached the top one percent of @RealTryHackMe. That was one of my goals for this year, so congratulations to me! Now, I have set my sights higher. I want to reach the top one thousand rank on TryHackMe.
Something extraordinary happened today. I was in the GingerHacker Initiative Discord community chatting with the founder. Since I spent my savings on the TryHackMe premium annual subscription, I told him how I'm preparing for SEC1 because it's practical and more affordable than Security+. He immediately offered to sponsor my certification to help me progress in my career. He decided to sponsor both SEC0 and SEC1. Shout out to the #GingerHacker!
It was a crazy and wonderful day! Also, I submitted the speller problem, and now I'm moving to week six.
Python rocks! 💪
Hack w/ Me - Episode 2 is LIVE
Check it out on all major platforms (Substack preferred 😉)
https://digitaldopaminellc.substack.com/p/hack-w-me-episode-2-search-skills
#hackwithme #tryhackme #cybersecurity #learning #fyp #explorepage #digitaldopamine #podcast
Hack w/ Me Episode 2: Search Skills
Watch now (23 mins) | Learn to efficiently search the Internet as well as use specialized search engines and technical docs
Hello, again 
Today, I started working through the network analysis rooms on TryHackMe. I used Wireshark to analyze PCAP files, which went smoothly since I have experience with it. However, I learned how to use statistics more effectively.
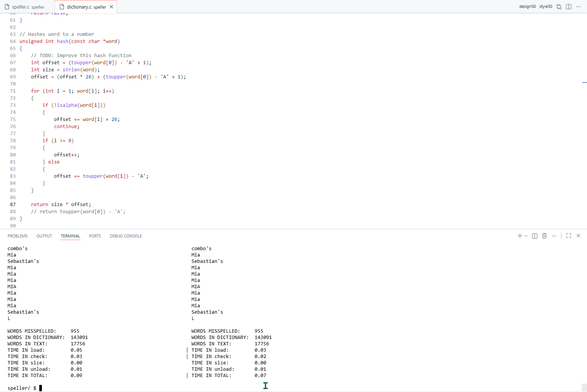
Lastly, I found a way to reduce collisions using a better hashing function. Instead of using just the first character to build the hash table, I multiplied the characters to increase entropy. I'm only six seconds behind the staff algorithm.
I also found a way to handle the apostrophe. Since I subtract 65 from the characters, the result is negative, which leads to a segmentation fault. I simply used a conditional statement to handle it.