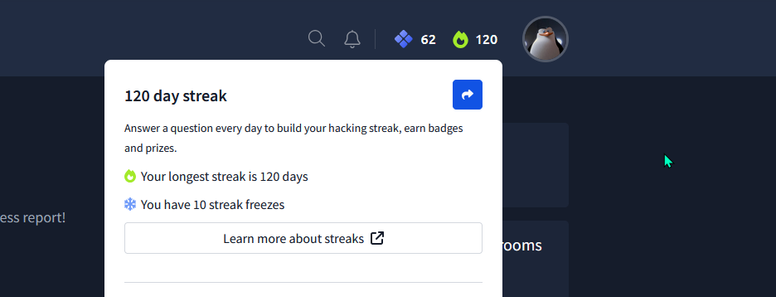
Hello, again, again, and again! 
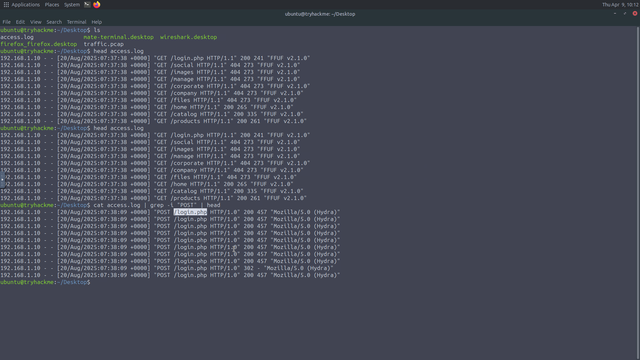
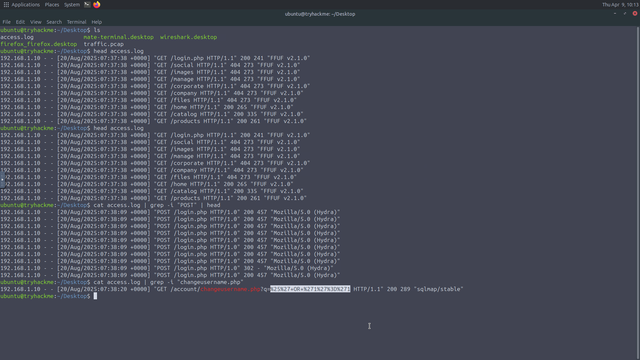
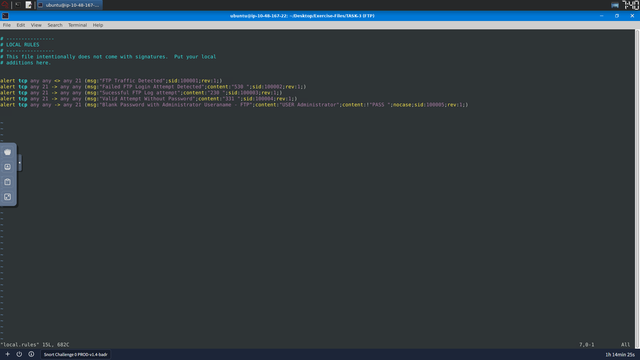
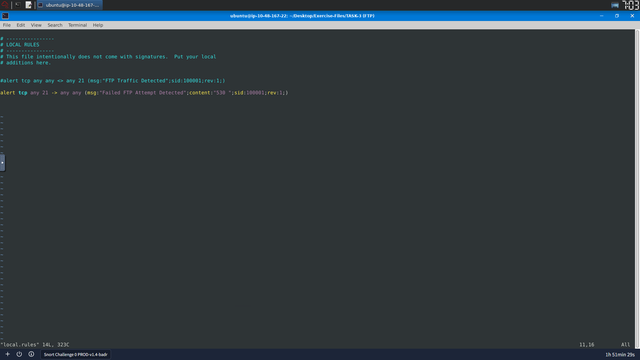
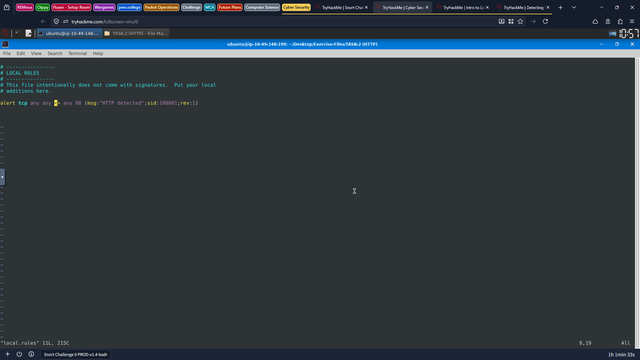
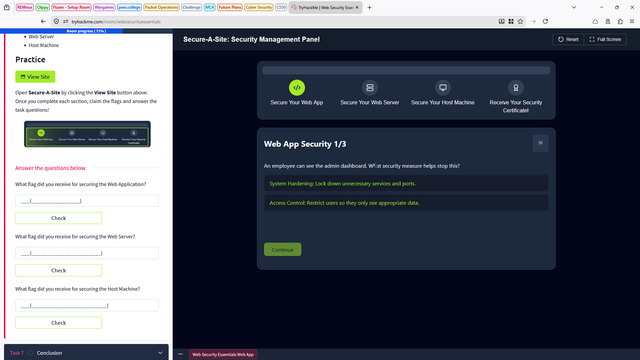
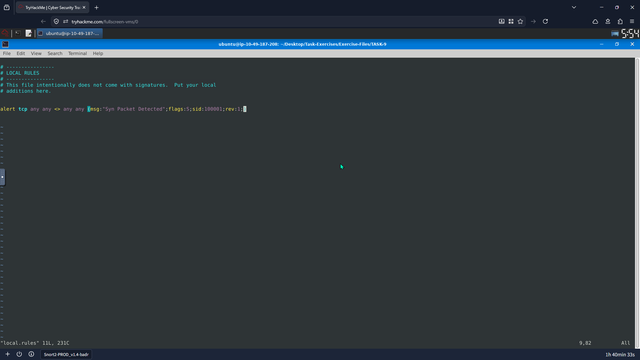
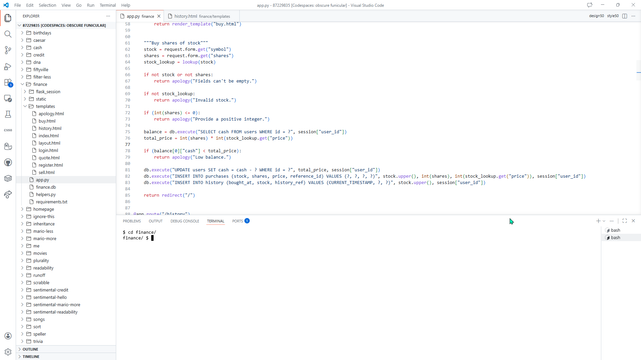
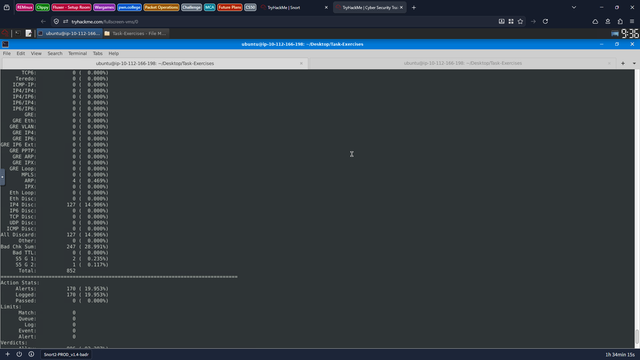
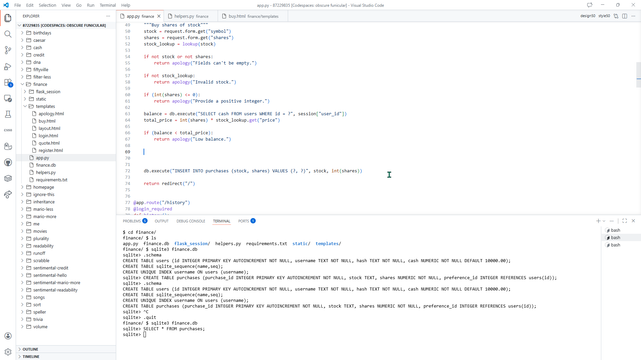
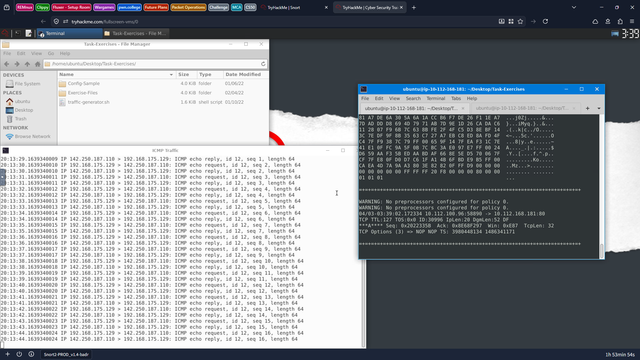
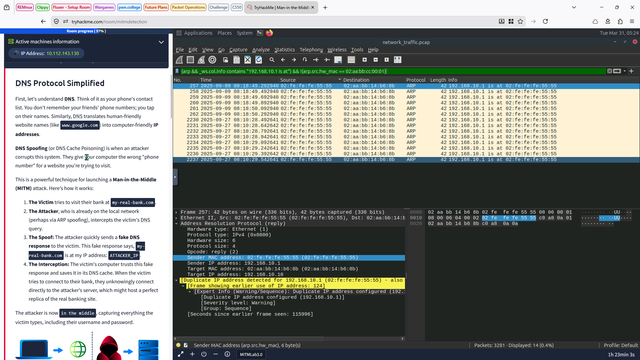
Today, I completed learning how to detect server-side attacks from /var/log. I also found a way to use different parts of the logs, such as the user agent, to identify automated tools being used.
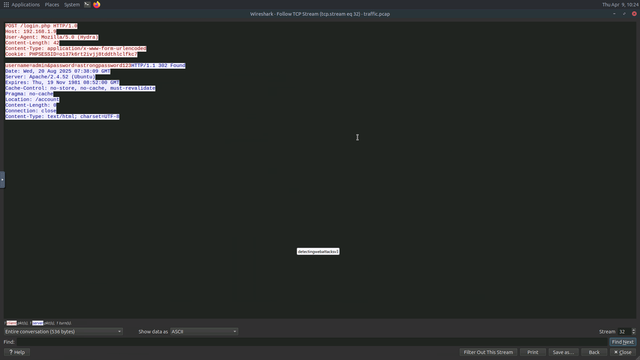
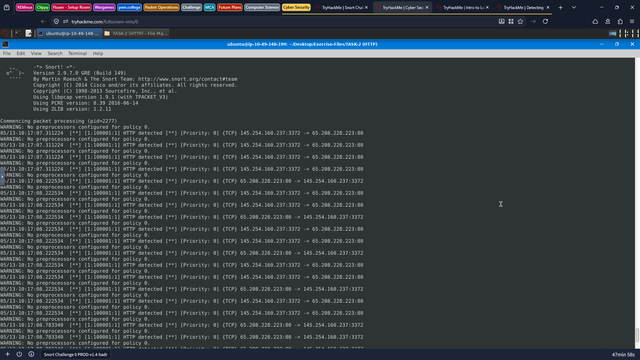
I also used Wireshark to analyze a brute-force attack and successfully recovered the password.
Then I started studying deep learning for my final-year exams, and I think I’m going to pause my 100 Days of Cybersecurity until my exams are over. 💪😭