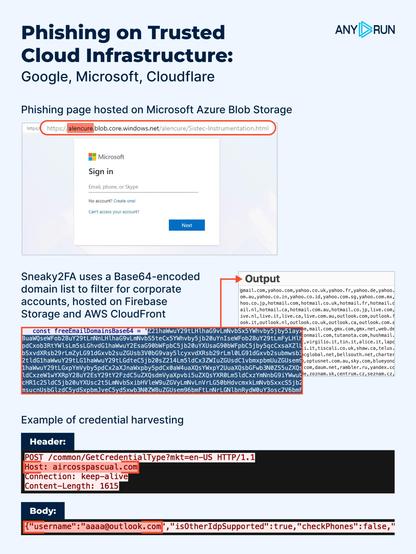
⚠️ Enterprise #phishing is now abusing Microsoft & Google Cloud. Trusted domains don’t get flagged by common detection tools, leaving companies exposed.
❗ #Sneaky2FA specifically targets corporate emails. See the analysis session and gather #IOCs: https://app.any.run/tasks/96dbe668-1be7-4001-be2c-edec54df09f7/?utm_source=mastodon&utm_medium=post&utm_campaign=enterprise_phishing_analysis_case&utm_term=120226&utm_content=linktoservice
Learn how these attacks work and what it takes for SOC teams to detect them: https://any.run/cybersecurity-blog/enterprise-phishing-analysis/?utm_source=mastodon&utm_medium=post&utm_campaign=enterprise_phishing_analysis_case&utm_term=120226&utm_content=linktoblog