«GITLAB DISCOVERS WIDESPREAD NPM SUPPLY CHAIN ATTACK»
🟠 [https://about.gitlab.com/blog/gitlab-discovers-widespread-npm-supply-chain-attack/]
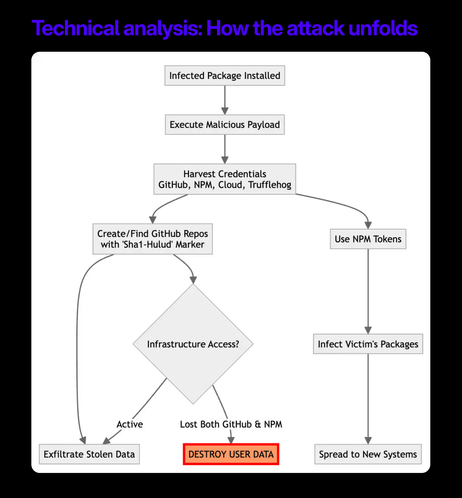
Это был, конечно, тяжёлый год для «npm», но этот "призыв Шаи-Хулуда" – одна из самых внезапных и отчасти красивых отссылок к «Dune».
Тот случай, когда смотришь на вирусную гадость и думаешь не "фу, какая вирусная гадость", а "ля, а как прикольно придумано".