RE: https://mastodon.social/@tdpauw/116709030423523606
"Yet, at the boundaries, the organisation must adapt and respond to changes in the environment. Therefore, it has to be open to environmental signals. As such, at its boundaries, it is an open system."
...
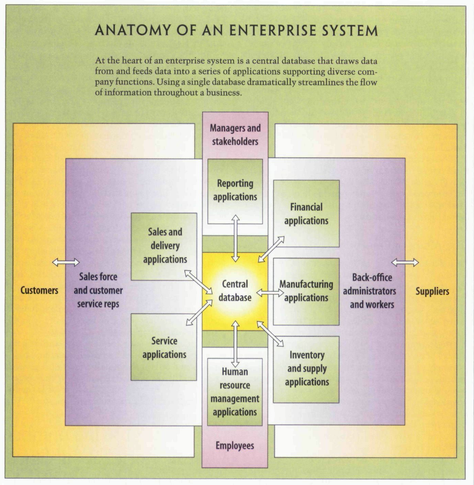
"While Emery & Trist define the external textures and Thompson explains the organisational structure to survive the environment and isolate the core work, Jay R. Galbraith articulates organisation design using a micro-level dimension: the flow of information."