#SmartApeSG #RemcosRAT #Stealc #SecTopRAT
https://isc.sans.edu/diary/32826
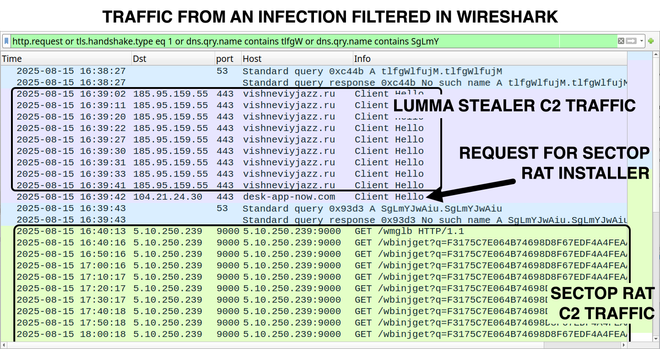
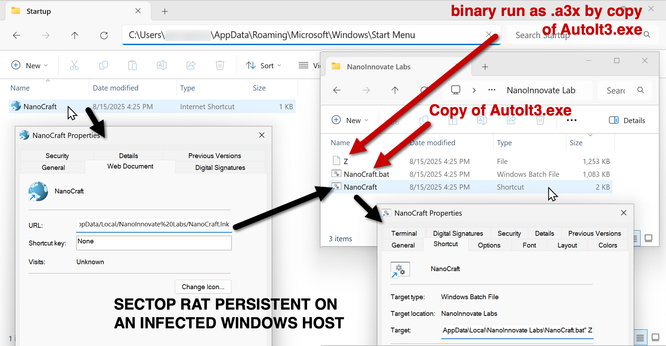
2025-08-15 (Friday): Here are some images from a post I wrote for my employer on other social media platforms.
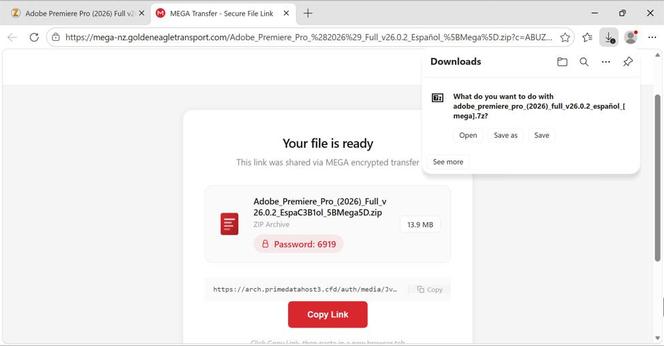
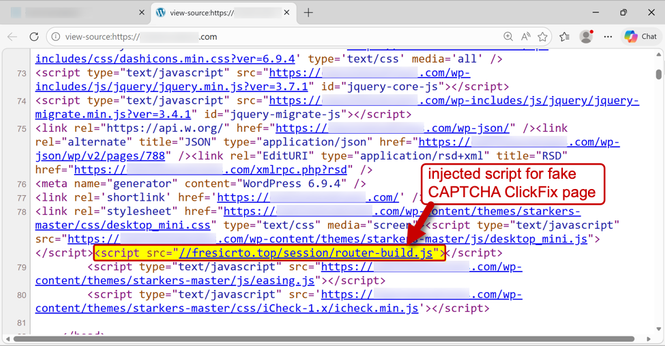
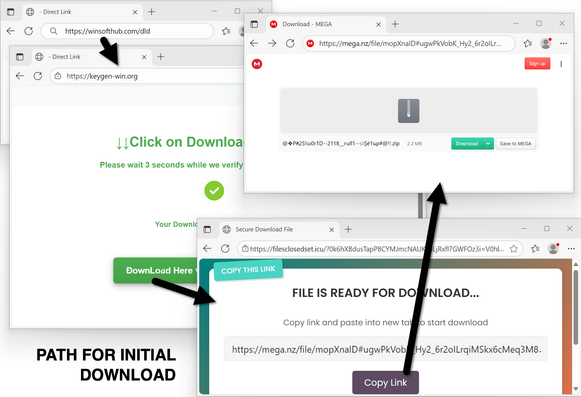
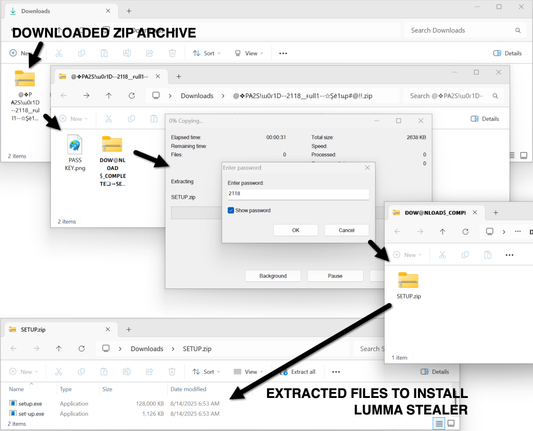
This is from a #LummaStealer infection that led to #SectopRAT (#ArechClient2).
A #pcap of the infection traffc, along with the associated #malware and artifacts are available at https://www.malware-traffic-analysis.net/2025/08/15/index.html
We've observed an interesting infection chain ⛓️ in the wild, starting with #LummaStealer spread through a fake gaming website and resulting in #Latrodectus and #SectopRat 🪲🔍👀
See below for more ⬇️
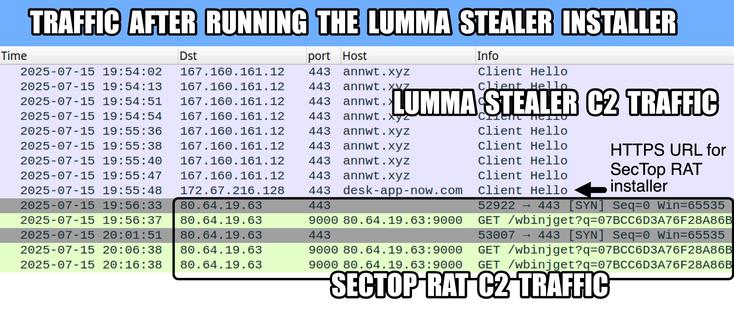
2025-07-15 (Tuesday): #LummaStealer infection with #SecTopRAT.
A #pcap of the #Lumma traffic and #SecTop #RAT activity, the #malware/artifacts from an infection, and the associated IOCs are available at https://www.malware-traffic-analysis.net/2025/07/15/index.html
#D3F@ckloader #IDATLoader #SecTopRAT
https://thedfirreport.com/2025/03/31/fake-zoom-ends-in-blacksuit-ransomware/
Enterprise networks were targeted in a campaign that involved SectopRAT and the deployment of BlackSuit ransomware via a trojanized Zoom installer.
Been awhile since the last #ArechClient2 / #SectopRAT #malware #infrastructure update. Let's take a look:
A new cluster has formed in Germany using HETZNER-AS (24940):
/167.235.102.163
/144.76.163.55 on port 15648 instead of 15647 for comms
/144.76.163.20 as above
Back in early May a new IP, this time in North Holland was observed: /185.73.125.96 - XHOST-INTERNET-SOLUTIONS (208091). It remains active.
A number of new Russian IPs have been added with Prospero:
/91.215.85.23
/91.215.85.26
And Medialand:
/45.141.87.16
/45.141.87.218
A number of IPs previously tracked have either gone offline completely or have stopped serving the "EncryptionStatus" banner:
/194.26.135.180
/152.89.217.229
/176.111.174.142
/2.57.149.77
/185.161.248.159