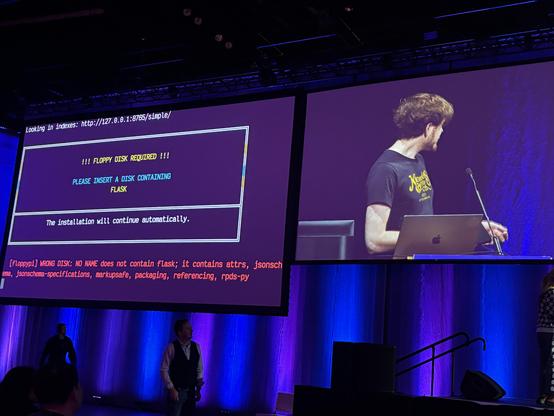
The PSF's PyPI Safety and Security Engineer, @miketheman, is giving a keynote at OpenSSF Community Day this Thursday! "Anatomy of a Phishing Campaign" is a deep dive into the 2025 PyPI phishing attack, how it worked, and what stopped it.
Thu May 21 @ 9:20am CDT 👉 https://openssfcdna2026.sched.com/event/2I44z
#Python #PyPI #SupplyChain #Security
https://openssfcdna2026.sched.com/event/2I44z