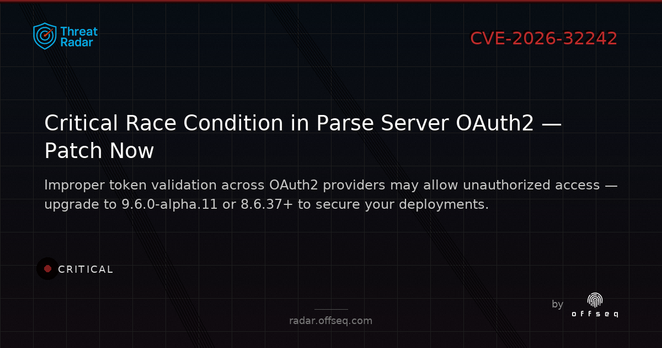
🚨 CVE-2026-32242: CRITICAL race condition in parse-server (>=9.0.0 <9.6.0-alpha.11, <8.6.37) lets OAuth2 tokens be validated against wrong provider configs. Patch to 9.6.0-alpha.11/8.6.37! https://radar.offseq.com/threat/cve-2026-32242-cwe-362-concurrent-execution-using--7a67bf5f #OffSeq #parseServer #OAuth2 #RaceCondition
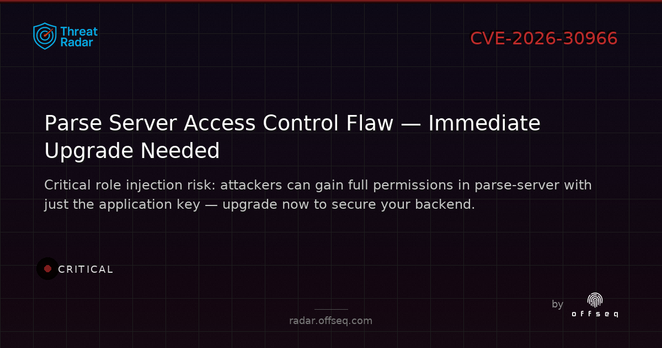
🚨 CRITICAL: CVE-2026-30966 in parse-server (<9.5.2-alpha.7, <8.6.20) lets attackers gain any role via REST/GraphQL with just the app key. Upgrade now and restrict API access! Full details: https://radar.offseq.com/threat/cve-2026-30966-cwe-284-improper-access-control-in--321de92a #OffSeq #parseServer #CVE202630966 #infosec
🚨 CRITICAL: parse-server (<8.6.10, <9.5.0-alpha.11) has CWE-287 improper authentication (CVE-2026-30863). JWT audience check skipped by default; attackers can impersonate users. Patch or set audience now. https://radar.offseq.com/threat/cve-2026-30863-cwe-287-improper-authentication-in--0b463399 #OffSeq #CVE202630863 #ParseServer #infosec
🚨 CRITICAL: CVE-2026-27804 in parse-server allows attackers to forge Google auth tokens (alg: none accepted)! Versions <8.6.3 & <9.1.1-alpha.4 at risk. Upgrade or disable Google auth now. https://radar.offseq.com/threat/cve-2026-27804-cwe-327-use-of-a-broken-or-risky-cr-9a87af7c #OffSeq #ParseServer #JWT #CVE202627804