salute to the wikipedian who wrote a new English language article for this Indonesian artist S. Sudjojono in the last few days and already nominated themselves for Good Article status. I need that kind of work ethic 🥸
https://en.wikipedia.org/wiki/S._Sudjojono
Apple's 398-day limit exempts private CAs. Most people stopped reading there.
There's a second Apple requirement: all TLS certs, 825 days max. Safari silently rejects anything longer. No bypass, no details.
https://www.certkit.io/blog/apple-doesnt-care-who-signed-your-certificate
Are we self-sovereign PKI yet?
Are we self-sovereign PKI yet?
PSA: You don't need a private CA for internal SSL certificates.
The CA doesn't connect to your server. It checks a DNS record. Your server can be completely unreachable from the internet.
https://www.certkit.io/blog/private-pki-internal-infrastructure
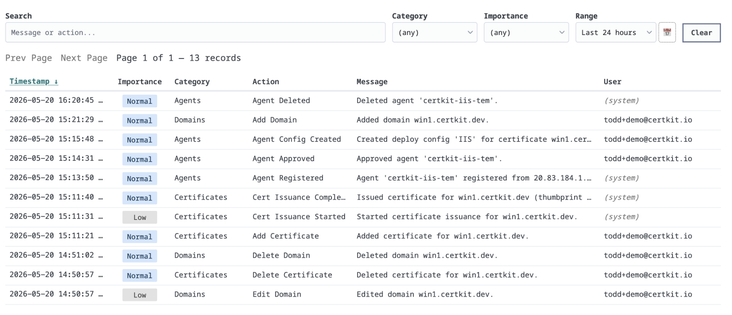
Compliance audits ask who touched your certificates, when, and why.
CertKit now captures every certificate action with timestamps and user attribution. Importance flags let you cut through routine events to the ones with real consequences.
https://malware.news/t/vulnerability-in-szafirhost-software/107036

Vulnerability in SzafirHost software
Unrestricted Upload of File with Dangerous Type vulnerability (CVE-2026-44088) has been found in SzafirHost software. Introduction to Malware Binary Triage (IMBT) Course Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor. Enroll Now and Save 10%: Coupon Code MWNEWS10 Note: Affiliate link – your enrollment helps support this platform at no extra cost to you. Article Link: Vulnerability in SzafirHost software | CERT Polska
TLSS или portable pki service в кармане
Сегодня я бы хотел рассказать о небольшом проекте, который тянется немного, немало, около двух лет. Я назвал его TLSS, или TLS Service — карманный pki сервис.
Hackers managed to trick DigiCert into issuing legitimate certificates — then used them to sign malware. 🔏
When trust infrastructure itself becomes a pivot point, the whole "just check the cert" reflex gets a lot more complicated.
A good reminder that certificate validation is necessary, but not sufficient. #infosec #PKI #malware
https://hackread.com/hackers-digicert-issue-certificates-sign-malware/