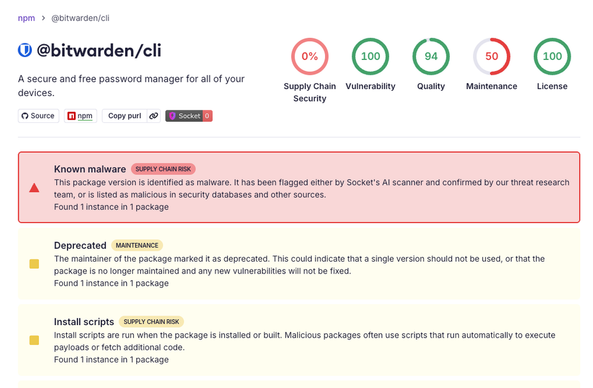
https://socket.dev/blog/bitwarden-cli-compromised #Bitwarden #SupplyChain #SocketResearch #npmSecurity #HackNews #HackerNews #ngated
https://socket.dev/blog/bitwarden-cli-compromised #Bitwarden #SupplyChain #SocketResearch #npmSecurity #HackNews #HackerNews #ngated
Axios npm Account Hijacked, Malware Injected
Axios npm account hijacked, malware injected into popular JavaScript library. Developers using versions 1.14.1 or 0.30.4 are at risk. Learn how to protect your code.
#AxiosAttack, #npmSecurity, #JavaScriptMalware, #CyberSecurity, #SoftwareSupplyChain
https://newsletter.tf/axios-npm-malware-attack-developers-risk/
Malicious code was put into the popular Axios JavaScript library for 3 hours. This is a new risk for developers using npm.
#AxiosAttack, #npmSecurity, #JavaScriptMalware, #CyberSecurity, #SoftwareSupplyChain
https://newsletter.tf/axios-npm-malware-attack-developers-risk/
[Claude Code 소스 코드가 npm 레지스트리 맵 파일을 통해 유출
Anthropic의 Claude Code CLI 소스 코드가 npm 레지스트리 내 .map 파일을 통해 유출된 사례가 보고되었다. .map 파일은 소스 코드의 디버깅 정보를 포함하여 원본 소스 코드를 복원 가능한 형태로 제공할 수 있어, 보안상 심각한 문제로 평가된다. 이 사건은 오픈소스 프로젝트나 클라우드 기반 AI 도구 개발 시 보안 취약점 관리와 소스 코드 유출 방지 전략의 중요성을 강조한다.
https://news.hada.io/topic?id=28059
#anthropic #claudecode #sourcecodeleak #npmsecurity #aisecurity
A malicious npm package is stealing WhatsApp messages — a sharp reminder that the software supply chain can betray even trusted platforms. Verify dependencies, always. 📦🔓 #SupplyChainRisk #NPMSecurity
https://www.theregister.com/2025/12/22/whatsapp_npm_package_message_steal/
https://www.koi.ai/blog/npm-package-with-56k-downloads-malware-stealing-whatsapp-messages #NPMsecurity #WhatsAppprivacy #codingrisks #trustissues #cybersecurity #HackerNews #ngated
A malicious npm package factory is churning out contagious code — proving the software supply chain can be poisoned at the source. Developers must verify every dependency. 🧩⚠️ #NPMSecurity #SupplyChainRisk
https://www.darkreading.com/application-security/contagious-interview-malicious-npm-package-factory
Moving Beyond the NPM elliptic Package
If you're in a hurry, head on over to soatok/elliptic-to-noble and follow the instructions in the README in order to remove the elliptic package from your project and all dependencies in node_modules. Art: CMYKat Why replace the elliptic package? Yesterday, the Trail of Bits blog published a post about finding cryptographic bugs in the elliptic library (a Javascript package on NPM) by using the Wycheproof.
http://soatok.blog/2025/11/19/moving-beyond-the-npm-elliptic-package/
#npm #crypto #cryptography #elliptic #security #infosec #cve #mitigation #appsec #javascript #js #npm #npmsecurity #npmpackages
Over 46,000 fake npm packages flood the ecosystem — attackers are poisoning the software supply chain at scale. Developers must verify before they install. 📦⚠️ #SoftwareSupplyChain #NPMSecurity
https://thehackernews.com/2025/11/over-46000-fake-npm-packages-flood.html
🚨 10 npm packages found deploying a multi-stage credential harvester.
Fake CAPTCHAs, IP fingerprinting, and PyInstaller malware targeting Windows, macOS, Linux - all under typosquatted names like typescriptjs and etherdjs.
💬 How are you strengthening your open-source dependency vetting?
Follow @technadu for daily infosec intel and malware investigations.
#CyberSecurity #SupplyChainAttack #NPMSecurity #DevSecOps #ThreatIntelligence #CredentialTheftattacks