Mini Shai-Hulud Strikes Again: 314 npm Packages Compromised
https://safedep.io/mini-shai-hulud-strikes-again-314-npm-packages-compromised/
#HackerNews #MiniShaiHulud #npmSecurity #CyberThreats #PackageCompromise #SoftwareVulnerability
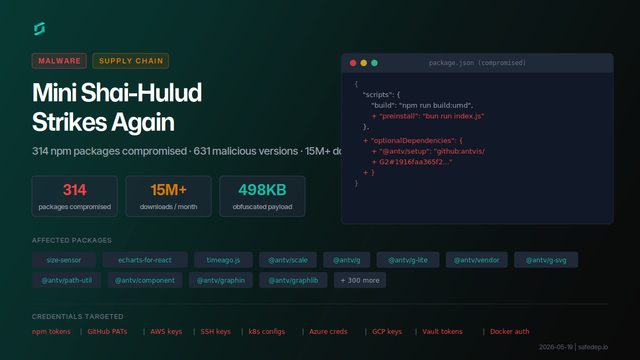
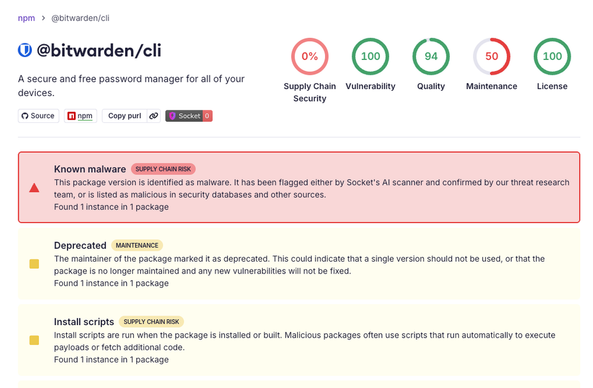
Mini Shai-Hulud Strikes Again: 317 npm Packages Compromised
A compromised npm maintainer account published 637 malicious versions across 317 packages including size-sensor, echarts-for-react, timeago.js, and hundreds of @antv scoped packages, affecting 15M+ monthly downloads.