Oh but it is also kinda interesting that when I specifically asked about an example for such a "corrupted file" and a diff I didn't get any response at all.
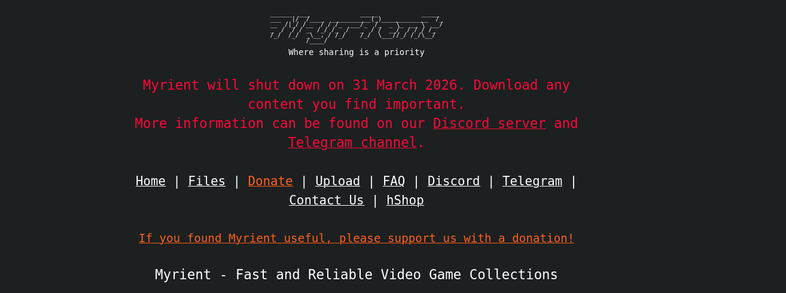
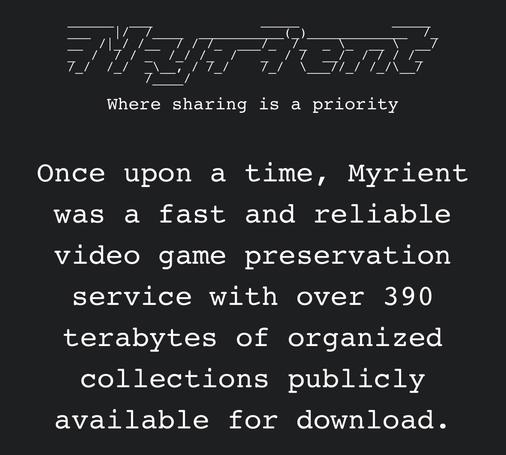
So anyone know what all of this is about?
Esp. because some mentioned them injecting or modifying the files I'm now also kinda interested in this from a #infosec perspective...
 ¯\_ (ツ) _/¯
¯\_ (ツ) _/¯