🚨 Update Your Detection Rules: New In-Memory Loader
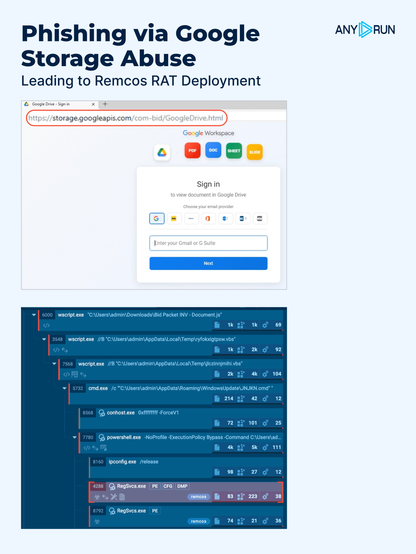
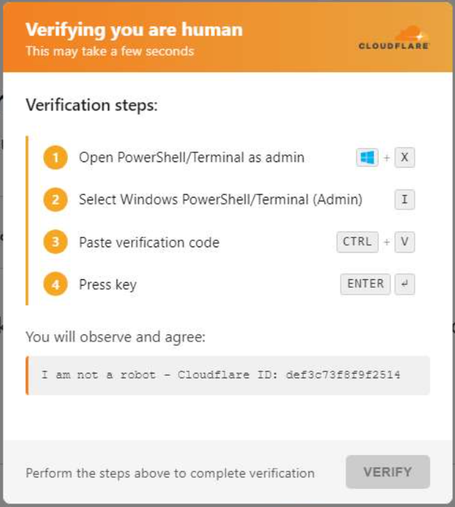
We caught a highly evasive #HanGhost loader, designed to bypass traditional detection through layered obfuscation and in-memory execution. This activity targets corporate users handling payments, logistics, and contract workflows, expanding exposure across critical operations.
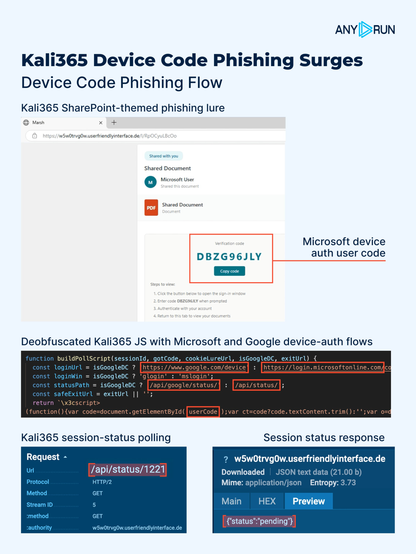
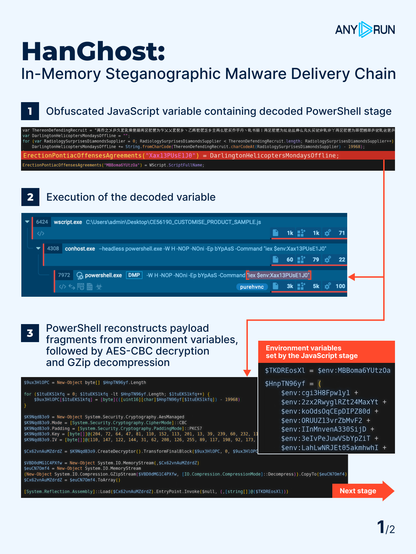
⚠️ The delivery chain combines obfuscated JavaScript, hidden PowerShell execution, and environment-variable staging.
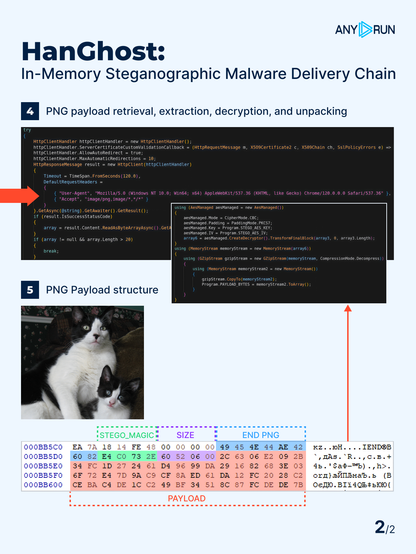
In the second stage, the loader retrieves an image file and extracts an encrypted payload embedded at the end of the file, combining steganography with in-memory loading and making detection significantly harder ❗️
👾 The loader is used to deliver multiple malware families: #PureHVNC, #XWorm, #Meduza, #AgentTesla, and #Phantom, with some chains also deploying #UltraVNC, extending the impact from initial access to persistent remote control.
⚡️#ANYRUN Sandbox allows analysts to reconstruct the full execution chain, helping confirm complex multi-stage activity earlier and reduce MTTR.
🔗 JavaScript-to-Payload execution chain:
JS ➡️ PowerShell ➡️ in-memory .NET assembly ➡️ PNG payload ➡️ Malware
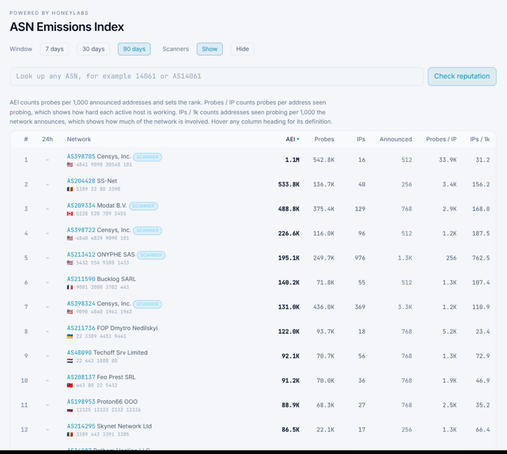
📈 The campaign shows wave-based activity, indicating ongoing development and scaling:
March 26 — early cluster
April 1–2 — first large multi-family wave
April 3 — focused wave (PureHVNC / AgentTesla / Phantom)
April 6 — PureHVNC-heavy activity
April 7 — new peak with split between PureHVNC and XWorm/Meduza clusters
April 8 — multi-family wave (PureHVNC / Phantom / AgentTesla)
April 9–13 — more focused wave dominated by PureHVNC, with Phantom, DarkCloud, Formbook, and Meduza also present
👨💻 See the analysis session and collect #IOCs to speed up detection and response: https://app.any.run/tasks/cc26155e-e8e9-442b-b000-8d1a1435e7db?utm_source=mastodon&utm_medium=post&utm_campaign=hanghost&utm_content=linktoservice&utm_term=130426
🔍 Use this TI Lookup query to pivot from IOCs, review related activity, and validate your detection coverage: https://intelligence.any.run/analysis/lookup?utm_source=mastodon&utm_medium=post&utm_campaign=hanghost&utm_content=linktotilookup&utm_term=130426#%7B%2522query%2522:%2522commandLine:%255C%2522bYPaSS%2520-Command%2520*iex%2520$env:%255C%2522%2522,%2522dateRange%2522:180%7D%20
👨💻 Equip your SOC with faster decisions and lower workload. See how #ANYRUN fits your workflows: https://any.run/enterprise/?utm_source=mastodon&utm_medium=post&utm_campaign=hanghost&utm_content=linktoenterprise&utm_term=130426
#cybersecurity #infosec