🚨 𝗠𝟯𝟲𝟱 𝗔𝗰𝗰𝗼𝘂𝗻𝘁 𝗧𝗮𝗸𝗲𝗼𝘃𝗲𝗿 𝗪𝗶𝘁𝗵𝗼𝘂𝘁 𝗖𝗿𝗲𝗱𝗲𝗻𝘁𝗶𝗮𝗹 𝗧𝗵𝗲𝗳𝘁: 𝗦𝘂𝗿𝗴𝗲 𝗶𝗻 𝗢𝗔𝘂𝘁𝗵 𝗣𝗵𝗶𝘀𝗵𝗶𝗻𝗴
We’re seeing a spike in activity from a #phishing campaign abusing Microsoft’s OAuth Device Code flow, with 180+ phishing URLs detected in just one week ⚠️
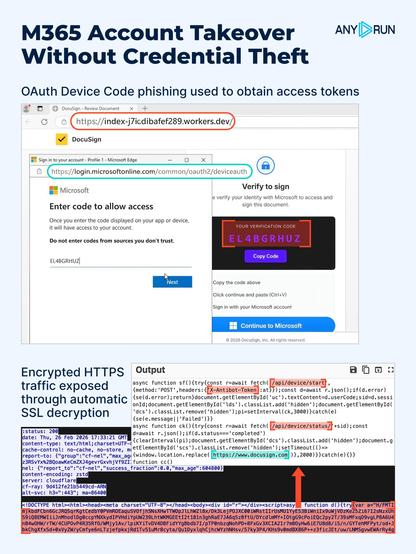
Attackers display a verification code and ask the victim to enter it on microsoft[.]com/devicelogin. Microsoft then issues OAuth tokens directly to the attacker, granting access to M365 resources without compromising credentials on the phishing page.
❗️ This shifts the risk from credential harvesting to token abuse. Because it runs over encrypted HTTPS, the activity blends into normal web traffic, delaying detection, extending investigations, and increasing escalation pressure. The window for early response keeps shrinking.
⚡️ #ANYRUN Sandbox now automatically decrypts HTTPS traffic by extracting SSL keys directly from process memory, without certificate substitution. This gives SOC teams wider phishing coverage, faster confirmation by Tier 2 and Tier 3 analysts, and improved MTTD & MTTR.
✅ In this case, SSL decryption exposed hidden JavaScript and revealed high-confidence tool-specific network #IOCs such as /api/device/start, /api/device/status/*, and the X-Antibot-Token header, which become high-signal when observed in HTTP requests to non-legitimate hosts.
👨💻 See analysis session: https://app.any.run/tasks/885afc1c-b616-46d7-9bc3-81185ee07fe3?utm_source=mastodon&utm_medium=post&utm_campaign=oauth_phishing_surge&utm_content=linktoservice&utm_term=040326
🔍 Use this TI Lookup query to review related activity and validate your detection coverage: https://intelligence.any.run/analysis/lookup?utm_source=mastodon&utm_medium=post&utm_campaign=oauth_phishing_surge&utm_content=linktotilookup&utm_term=040326#%7B%22query%22:%22threatName:%5C%22oauth-ms-phish%5C%22%22,%22dateRange%22:7%7D
🎯 Find the IOCs in the comments. A full breakdown of this campaign is coming soon, stay tuned.
⚡️ Encrypted traffic is no longer a blind spot. Learn how SSL decryption expands phishing detection and reduces risk: https://any.run/cybersecurity-blog/automatic-ssl-decryption/?utm_source=mastodon&utm_medium=post&utm_campaign=oauth_phishing_surge&utm_content=linktoblog&utm_term=040326