I spoke with @berniework for @CypherCon #HackerHistory
Bill had some great stories about how he started out helping his Dad and eventually found himself working at phone company trying to sell TV and a TV company trying to sell phones
It's a really fun story
https://hackerhistory.com/podcast/the-history-of-bill-bernard/
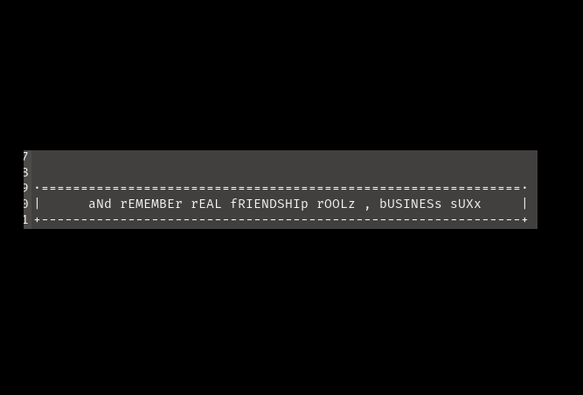
Blast from the past!
Here's a vintage recording from the @2600 Voice BBS (c. 1990s) featuring details on the Manchester meetup at the iconic Cyberia Internet Cafe on Oxford Road.
(Also includes details on Bristol and London meetings).
#2600 #BBS #RetroComputing #Manchester #HackerHistory #Cyberia
This episode of @CypherCon #HackerHistory we talk to Rebecca Jones about a journey from an Apple 2 in school to a career in security
There some great advice in this one plus it's a lot of fun
https://hackerhistory.com/podcast/the-history-of-rebecca-jones/
A new #HackerHistory is out!
This time we hear the story of Pyr0
Pyr0 tells us about a new upcoming conference all about hacker history, NaClCON
Then we hear about a lot of awesome hacker history
It's a great story!

The history of Pyr0 - Hacker History Podcast
Hacker History sits down with Luke McOmie, AKA Pyr0, to talk about a new conference about hacker history, as well as his history. Pyr0 tells us all about NaClCON. It's a conference dedicated to the stories of the hackers themselves. Go register if you're interested ... while you still have time! Pyr0 then tells us […]
@mattblaze
RE
one of the early, pioneering #phonephreaks
Yea, I heard the #offthehook #2600oth radio #wbai and podcast folks talk about him over the years, since the 1980s.
@OffTheHook
Thx for the reminder about the doc at #sundancefilmfestival
"Josef Carl Engressia Jr., aka: Whistler, later known as Joybubbles...He could whistle a perfect 2600 Hz tone"
#hackers #hackerhistory
A new @CypherCon #HackerHistory is out!
This time I'm talking to Dr. Laura Scherling, EdD, Rachael Tubbs, and Ben Schmerler. Laura wrote a book titled "The Future of Hacking" and Rachael and Ben join us because IoT Village is ten years old (time sure does fly), and are part of Laura's book.
It's a super fun conversation where we cover some past, present, and future of hacking
https://hackerhistory.com/podcast/the-history-of-laura-rachael-and-ben/
I had a chat with David Bernstein on the @CypherCon #HackerHistory podcast
David tells us all about his experience in emergency management. David has seen a ton of wild events, and has some really interesting commentary about how emergency management and infosec collide. David isn't what many would consider a traditional hacker, but it's clear he has had incredible impact over the years.
https://hackerhistory.com/podcast/the-history-of-david-bernstein/
The history of David Bernstein - Hacker History Podcast
Hacker History sits down with David Bernstein. We learn about David's past in emergency management. David has seen a ton of wild events, and has some really interesting commentary about how emergency management and infosec collide. David isn't what many would consider a traditional hacker, but it's clear he has had incredible impact over the […]