DomainTools Investigations | SecuritySnack - CloudFlare Anti-Security For Phishing
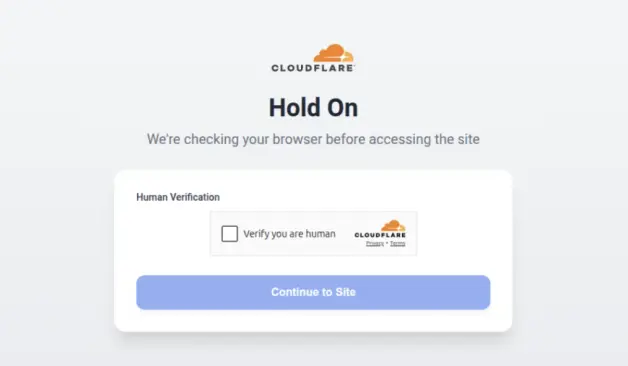
A Microsoft 365 credential harvesting campaign is exploiting CloudFlare's anti-bot and human verification features to evade detection. Learn how attackers use IP blocklists, user-agent filtering, and obfuscated scripts to bypass security scanners—and what it means for the industry.

 🏴☠️
🏴☠️



