⚡ Fresh Talk Alert for BSides Luxembourg 2026!
“𝗜𝗡𝗙𝗢𝗦𝗧𝗘𝗔𝗟𝗘𝗥 𝗘𝗠𝗨𝗟𝗔𝗧𝗜𝗢𝗡: 𝗩𝗔𝗟𝗜𝗗𝗔𝗧𝗜𝗡𝗚 𝗗𝗘𝗧𝗘𝗖𝗧𝗜𝗢𝗡 𝗢𝗙 𝗖𝗥𝗘𝗗𝗘𝗡𝗧𝗜𝗔𝗟 𝗧𝗛𝗘𝗙𝗧” – 𝗙𝗜𝗟𝗜𝗣𝗜 𝗣𝗜𝗥𝗘𝗦
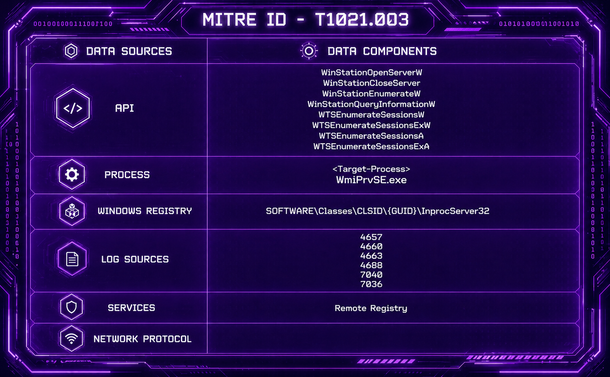
Infostealers remain one of the most widespread and damaging threats in today’s cyber landscape. In this practical session, Filipi Pires demonstrates how to emulate real infostealer behavior to test whether your security controls can actually detect credential theft and data exfiltration attempts.
The session includes live demonstrations covering browser credential theft, keylogging, clipboard monitoring, LSASS credential dumping, and validation of DLP and network monitoring controls. Attendees will gain practical insight into how attackers operate — and how defenders can validate their visibility and detection capabilities against modern credential theft techniques.
Filipi Pires is Head of Technical Advocacy at SCYTHE, DEF CON Red Team Village Director, BSides Porto Organizer, and an internationally recognized speaker specializing in red teaming, malware analysis, and offensive security.
📅 Conference Dates: 6–8 May 2026 | 09:00–18:00
📍 14, Porte de France, Esch-sur-Alzette, Luxembourg
🎟️ Tickets: https://2026.bsides.lu/tickets/
📅 Schedule: https://hackertracker.app/schedule?conf=BSIDESLUX2026
#BSidesLuxembourg2026 #Infostealer #CredentialTheft #RedTeam #DetectionEngineering #CyberSecurity #BlueTeam #DFIR