‘CanisterWorm’ Springs #Wiper Attack #Targeting #Iran
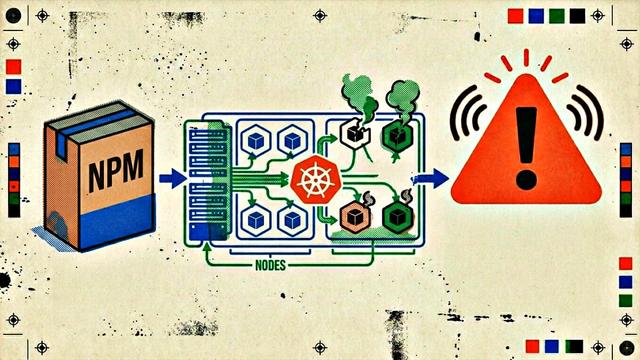
A financially motivated data theft and #extortion group is attempting to inject itself into the #Iranwar , unleashing a #worm that spreads through poorly secured cloud services and wipes data on infected systems that use Iran’s time zone or have #Farsi set as the default language.
#security #CanisterWorm
https://krebsonsecurity.com/2026/03/canisterworm-springs-wiper-attack-targeting-iran/