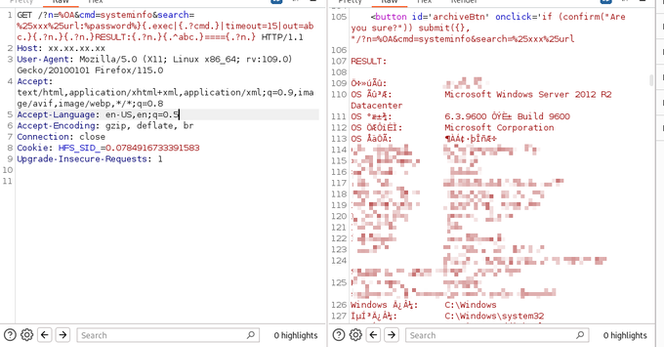
This is a destructive OPSEC failure.
PoC code is trivial to find along with a simple Censys query to uncover vulnerable hosts. The code itself supports a TXT file of URLs so....spray and pray method to find targets. Certain campaigns used #XMRig, GoThief, and backdoors like #Gh0stRAT and #PlugX.
It should go without saying to not make your file servers open to the public but some didn't get the memo.
#HFS #CVE202423692 #ThreatIntel