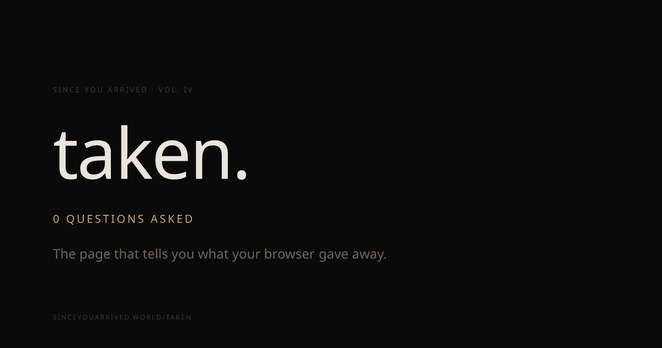
This website is great! This website is awful… It’s awful what it can easily do, great that they are teaching about web browser fingerprinting.
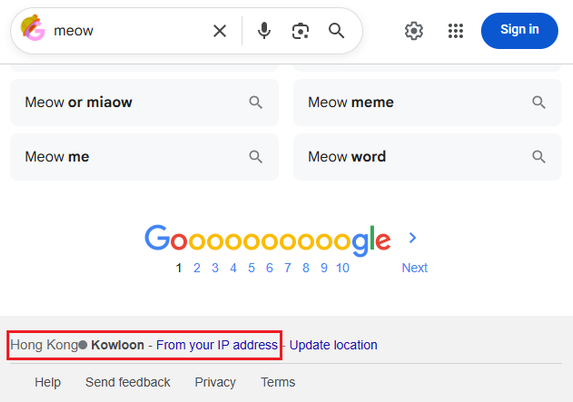
It looks like Google can track me in other ways.
Note that I never sign in to my Google account here, and I clear cookies, local storage, etc, every time I exit the browser. I do not use browser extensions like Location Guard.
Do I appear to be in Singapore? I'm not in Singapore right now.
Screenshot 1 was taken when not using incognito mode; Screenshot 2 was taken while using incognito mode.
#Google #Chrome lacks browser fingerprinting defenses • The Register
While #browserfingerprinting may have valid uses, it poses a significant privacy risk. And fingerprinting of this sort need not include much technical information at all. A study published in Nature last October found that just knowing the four websites an individual visits the most – a behavioral fingerprint as opposed to a browser fingerprint – is enough to identify 95 percent of people.
https://www.theregister.com/2026/04/16/google_chrome_lacks_browser_fingerprinting/
Google Chrome Fails to Thwart Browser Fingerprinting
If a browser claims to be safe but fails to block one of the easiest ways for advertisers to track you online, can it really be considered safe? Google Chrome, despite its reputation for security, surprisingly leaves users vulnerable to browser fingerprinting, a pervasive tracking method that can uniquely identify and follow you around…
#BrowserFingerprinting #GoogleChrome #OnlineTracking #Privacy #EmergingThreats
@axels my favorite tool doesn't exist.
In today's current online environment, if you don't want your online behavior following you around, you need to shake your device fingerprint. There's no way around that, really. For some people, this looks like a multi-login #browser for others, it's just using different browsers for different tasks. The #tech simply does not exist to allow the average consumer to stop trackers from following them everywhere they go on the #internet.
When an adversary can link your behavior across sites and sessions, that gives them the ability to build a comprehensive profile of who you are. Your hobbies, interests, schedule, habits, worries, and beliefs all crammed into one profile.
I've found that I can successfully make my device appear as another device by modifying HTTPS headers, #JavaScript, TLS fingerprint, and network telemetry values (like TTL, MSS, window size, etc.). This #privacy approach allows me to scrub my browsers native fingerprint and replace it with a new one.
The key is coherency, though, tools like fingerprintJS can detect mismatches between headers and JS advertised properties and flag the user as a bot. Though, browsers like #firefox, #brave, and #duckduckgo do a good job of mitigating many of these fingerprinting techniques.
I've developed some #opensource tooling to give users free control over their data.
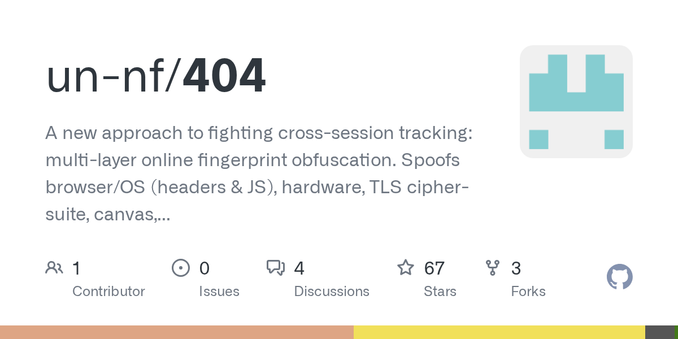
GitHub - un-nf/404: A new approach to fighting cross-session tracking: multi-layer online fingerprint obfuscation. Spoofs browser/OS (headers & JS), hardware, TLS cipher-suite, canvas, peripherals and much more.
A new approach to fighting cross-session tracking: multi-layer online fingerprint obfuscation. Spoofs browser/OS (headers & JS), hardware, TLS cipher-suite, canvas, peripherals and much more. -...
Are there any #Tor or #BrowserFingerprinting or traffic fingerprinting people in my wider network that have read the #MaybeNot paper?
How do these defenses relate to the work that Tor itself does to protect from traffic analysis? Would they be enough to prevent the sort of timing attacks that the wiki describes on the TorPlusVPN page?
Does anyone have more information on the research that that wiki page is referencing?
I am just diving into this topic, so be gentle please.
It's easy to assume a VPN keeps you private, but they're not effective against the most prevalent form of cross-site tracking: Browser Fingerprinting.
Our latest video covers what browser fingerprinting is in detail and what you can do to protect yourself from trackers, plus we spoke with @ruihildt from @mullvadnet for more info on what the top privacy browsers are doing about this problem.
https://www.privacyguides.org/videos/2025/09/12/what-is-browser-fingerprinting-and-how-to-stop-it/
 https://www.youtube.com/watch?v=v_50cBtSjyQ
https://www.youtube.com/watch?v=v_50cBtSjyQ https://neat.tube/w/2TQztsQGZ6ZPiJVSUtSDHa
https://neat.tube/w/2TQztsQGZ6ZPiJVSUtSDHa
#BrowserFingerprinting #MullvadBrowser #TorBrowser #BrowserFingerprint #AmIUnique #Fingerprinting #Privacy #Chrome #Firefox #PrivacyGuides #Video
What Is Browser Fingerprinting? (And How to Stop It!)
#Cybersecurity #BrowserFingerprinting
Last Friday @privacyguides released its second episode this year of This Week in Privacy! 🎤🔒✨
You can now watch it from our PeerTube instance!
Lots of very important topics being discussed in there: https://neat.tube/w/4ZCEWBfujAqHRRABNBhjB9
#PrivacyGuides #Privacy #Security #AgeVerification #BrowserFingerprinting
ChromeOS & Android Are Merging? | This Week in Privacy #10 (Jul. 18, 2025)
Thinks: Anyone yet seen Advertising inside a CAPTCHA/reCAPTCHA??
"Choose the brand that mows your lawn, picks up the kids from school, gets rid of unwanted facial hair, gets rid of embarrassing age spots, delivers the pizza"
———
'The First Early Evidence of
the Use of Browser Fingerprinting for Online Tracking'
https://engineering.jhu.edu/news/websites-are-tracking-you-via-browser-fingerprinting/