| Location | San Francisco |
| Github | https://github.com/stricaud |
Sebastien Tricaud
- 243 Followers
- 550 Following
- 92 Posts
Scattered Spider: Detection Engineering Dilemma - Detecteam
Scattered Spider is a hot topic. As a native English speaking group, it quickly grew as a threat to various organizations. Being a versatile threat actor, from data leak to ransomware deployment. It is described by various references, such as (but not limited to): https://www.cisa.gov/news-events/cybersecurity-advisories/aa23-320ahttps://reliaquest.com/blog/scattered-spider-attack-analysis-account-compromisehttps://www.attackiq.com/2025/05/29/emulating-scattered-spiderhttps://unit42.paloaltonetworks.com/muddled-libra-evolution-to-cloudhttps://cloud.google.com/blog/topics/threat-intelligence/unc3944-targets-saas-applicationshttps://www.tidalcyber.com/blog/scattered-spider-evolving-resilient-group-proves-need-for-constant-defender-vigilance Known Scattered Spider aliases are: 0ktapus, oktapus, UNC3944, Starfraud, muddled...
I'd like to share something nice that I am currently working on: A Landlock integration for Forgejo.
Landlock (https://landlock.io) lets userspace processes tell the kernel "hey kernel, please only let me access the following filesystem resources" (and it also supports sockets, etc. now).
My integration only limits unfettered access to arbitrary files. It needs a lot more yak shaving (refactoring, configurations, using the PATH variable for Git binaries) and time.
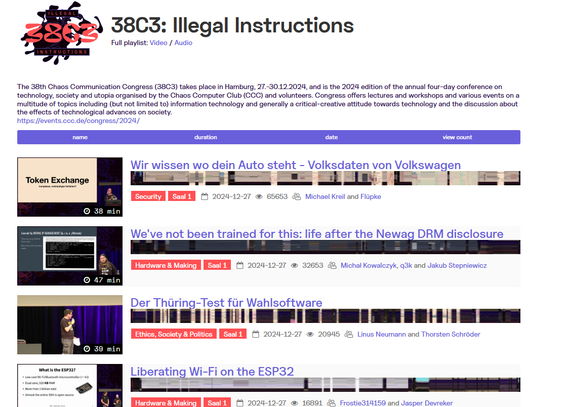
All videos from The 38th Chaos Communication Congress (38C3) 2024:
https://media.ccc.de/b/congress/2024
#cybersecurity #informationsecurity #hacking #exploitation #iOS #android #apple #exploitation #reverseengineering #vulnerability