| Website | https://www.romainthomas.fr |
| LIEF | https://lief.re |
| open-obfuscator | https://obfuscator.re |
Romain THOMAS
- 448 Followers
- 187 Following
- 29 Posts
I reverse engineered DexProtector, the security solution protecting applications like Revolut and other banking apps.
From custom ELF loaders to vtable hooking, here is an insight into how these protections work and their limitations.
New blog post on implementing patchelf-like functionalities using LIEF's Rust bindings:
The DWARF debug format is well-known for debugging executables,
but it is also an effective format for sharing reverse engineering information
across various tools, such as IDA, BinaryNinja, Ghidra, and Radare2.
In this blog post, I introduce a new high-level API in LIEF that allows the
creation of DWARF files. Additionally, I present two plugins designed to export
program information from Ghidra and BinaryNinja into a DWARF file.
https://lief.re/blog/2025-05-27-dwarf-editor/
(Bonus: The blog post includes a DWARF file detailing my reverse engineering work on DroidGuard)
Here we go: https://www.romainthomas.fr/post/25-04-windows-arm64-qbdi-fuzzing/
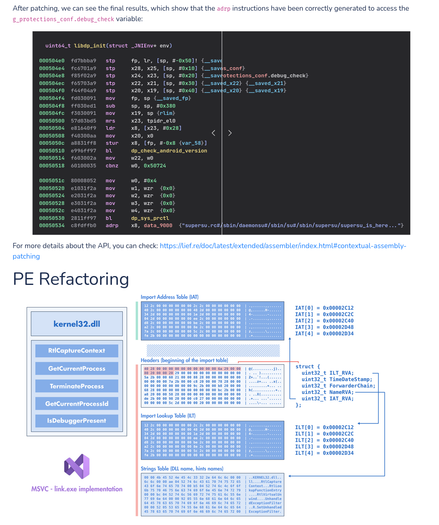
New updates in LIEF including better support for PE modifications and ARM64EC/ARM64X binaries.
Blog post: https://lief.re/blog/2025-02-16-arm64ec-pe-support/
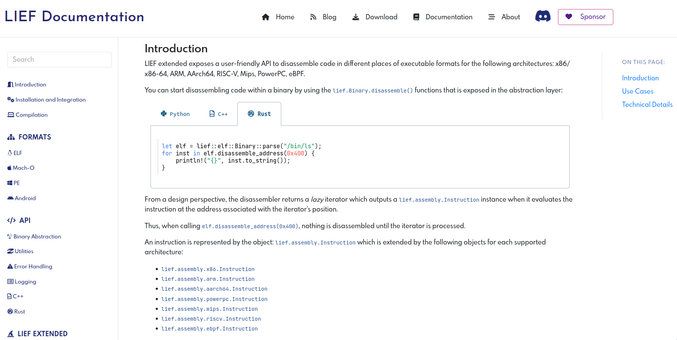
LIEF 0.16.0 is out featuring new (extended) capabilities like Dyld Shared Cache support, Assembler/disassembler, ...
I'm happy to share that LIEF (extended)
is now providing an API to disassemble code (backed by the LLVM MC layer).
This disassembler is integrated with other functionalities
like dyld shared cache support or DWARF debug info.
You can checkout https://lief.re/doc/latest/extended/disassembler/index.html for the details.
Extracting liblockdown.dylib from visionOS dyld shared cache and running it
with a DBI on macOS?
Challenge accepted!
📖 Blog: https://www.romainthomas.fr/post/24-09-apple-lockdown-dbi-lifting/
🎞️ Demo: https://www.youtube.com/watch?v=5L05OE5mL2o
⌨️ Code: https://github.com/romainthomas/visionOS-liblockdown