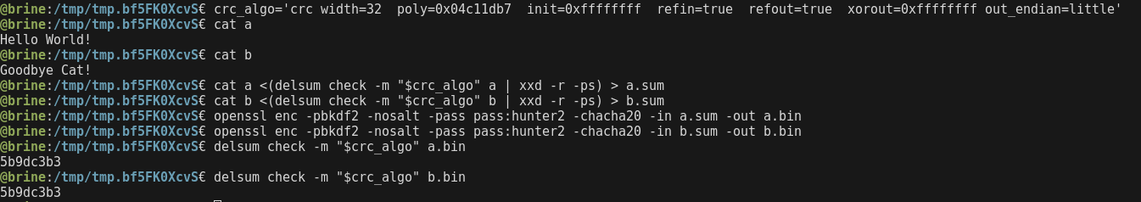
if you encrypt the resulting message with a stream cipher, the CRC of the message is cancelled out so you essentially get the CRC of the keystream. as a result, if you encrypt 2 different files of same length with CRC appended with the same (unsalted) key, you get the same CRC on the encrypted file
Travis Goodspeed
@travisgoodspeed
- 435 Followers
- 81 Following
- 26 Posts
@brouhaha Excellent! Please let me know if I'm missing any features that would help for the PLA decoding.
neat little fact about CRCs and stream ciphers: if you append a CRC to a message, you always get the same CRC.
if you encrypt the resulting message with a stream cipher, the CRC of the message is cancelled out so you essentially get the CRC of the keystream. as a result, if you encrypt 2 different files of same length with CRC appended with the same (unsalted) key, you get the same CRC on the encrypted file
if you encrypt the resulting message with a stream cipher, the CRC of the message is cancelled out so you essentially get the CRC of the keystream. as a result, if you encrypt 2 different files of same length with CRC appended with the same (unsalted) key, you get the same CRC on the encrypted file
Nifty 8051 reversing tool by @8051enthusiast, including a base address finder and recovery of symbol names for library functions. Proper comments, which are worth more than gold when you're trying to learn to do this stuff yourself.
Once upon a time in 1993 I was a teen, and I wrote a Pascal compiler for transputer. I was learning so many things. I've wrote an article about it, and released the code, along a newly coded transputer emulator 😉 #retro #transputer https://nanochess.org/pascal.html
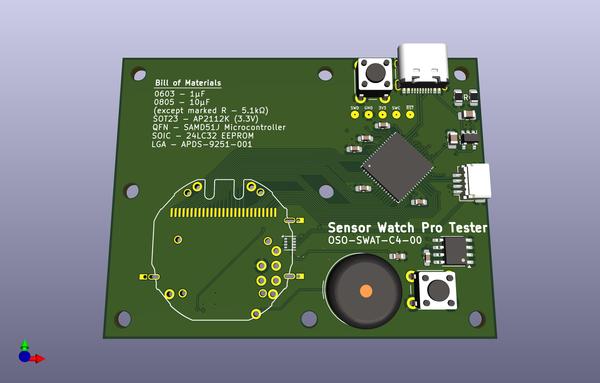
when it comes time to assemble this thing, future-joey owes me a beer for being so thoughtful
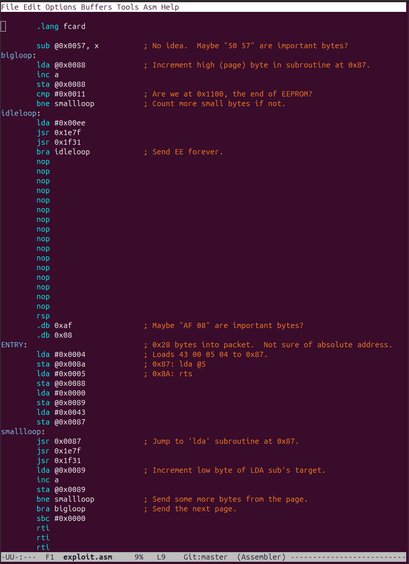
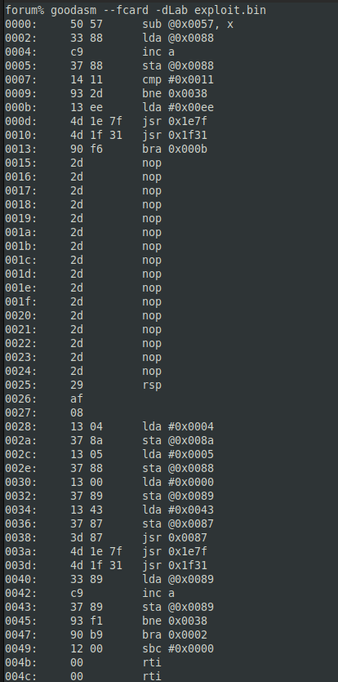
@akacastor Same thing as source code. I'm pretty sure the entry point is at 0x28 relative to the start of the packet, but neither AF08 nor 1200 make sense as a big endian return address, so I'm not quite sure what the absolute address is.
Thanks for your attention,
it was fun!
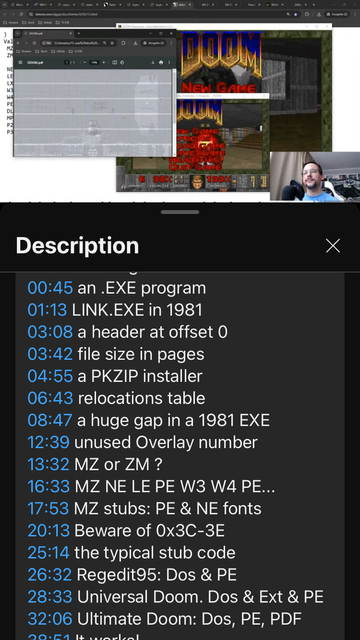
I crafted a working Doom polyglot:
Dos executable, Portable executable and PDF.
https://www.youtube.com/live/nG2RZrD4kAo?si=iyU-4ce8xTIfC3o6
it was fun!
I crafted a working Doom polyglot:
Dos executable, Portable executable and PDF.
https://www.youtube.com/live/nG2RZrD4kAo?si=iyU-4ce8xTIfC3o6
15 .EXE Dos program
@akacastor Tossed together an F-Card module for my assembler this evening. It looks reasonable for functions in ROM Page 0.
I'm not sure why they rewrite code in a subroutine at 0x87 when it's all in the zero page and easy to rewrite directly, without a subroutine.
Anyone interested in microcontroller exploits?
Here's how I started with a pair of protected 68HC705s and some blanks, and ended with a ROM dump.
(It is, of course, a fault injection attack)
https://www.philpem.me.uk/elec/security/68hc705c8_dump
https://github.com/philpem/68hc705_glitcher
Dumping a protected MC68HC705C8S
Dumping a protected MC68HC705C8S This is the writeup which goes with my 68HC705C8 Glitcher Github project. I'm involved with some of the reverse-engineering side of HackTV development, and as part of that I tear apart receivers so we can generate the data formats they need for e.g. EPG data and conditional-access. You can see some of that work in the
@travisgoodspeed in case you haven't seen this yet: https://aus.social/@projectgus/113777912133204503
Gus (@[email protected])
"Beyond BLE: Cracking Open the Black-Box of RF Microcontrollers" is a fascinating 38C3 technical reversing talk: undocumented functionality, custom processor ISAs, making an open source toolchain, etc. Also happy to see they sourced useful info from TI's patents. Disclosing your invention is supposed to be part of the bargain of patents, but increasingly obfuscated by companies writing their patents vaguer and vaguer... https://media.ccc.de/v/38c3-beyond-ble-cracking-open-the-black-box-of-rf-microcontrollers https://youtu.be/Qht3abt7Tx8 #reverseengineering #sdr