| https://twitter.com/thehellu |
Daniel Lunghi
- 263 Followers
- 109 Following
- 18 Posts
You can then use the VolumeID tool from Sysinternals to change the volume serial number of your virtual machine
https://learn.microsoft.com/en-us/sysinternals/downloads/volumeid
#APT
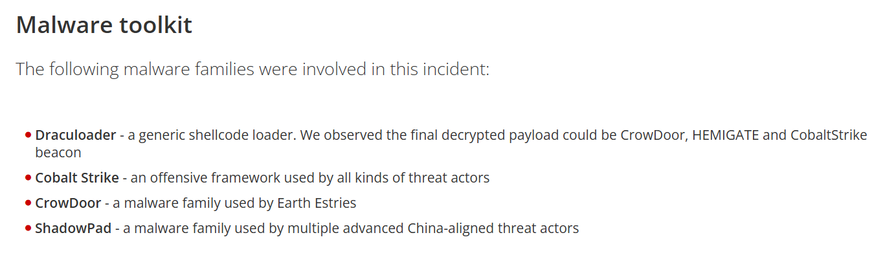
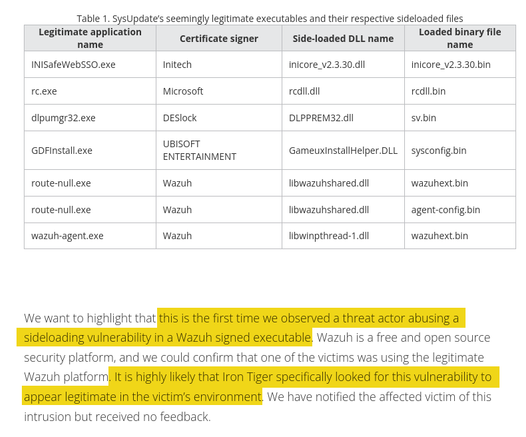
Orange Cyberdefense saw the same threat and named the ransomware "NailaoLocker" https://www.orangecyberdefense.com/global/blog/cert-news/meet-nailaolocker-a-ransomware-distributed-in-europe-by-shadowpad-and-plugx-backdoors They share interesting thoughts on the motivations of the ransomware deployment, although they don't have the final answer. We also saw no financial gain for the threat actor
Targets are spread among 5 continents, although some countries are targeted more heavily: one country had 11 of its government entities compromised. Previous victims are used to compromise new ones by abusing their infrastructure to send spear-phishing emails or host malware.
Their favorite malware toolkit are Reshell, a basic .NET backdoor, and Xdealer, also named Dinodas RAT, two custom malwares. They also use the infamous #CobaltStrike, #PlugX and #Shadowpad. Many of their offensive and post-exploitation tools are retrieved from public sources.
The slides https://virusbulletin.com/uploads/pdf/conference/vb2023/slides/Slides-Possible-supply-chain-attack-targeting-South-Asian-government-delivers-Shadowpad.pdf and paper https://virusbulletin.com/uploads/pdf/conference/vb2023/papers/Possible-supply-chain-attack-targeting-South-Asian-government-delivers-Shadowpad.pdf are also available. In addition to what we published in July in our blog, the paper details our failed attempts to attribute this attack based on custom malware families and their links to other advanced threat actors #threatintel
Possible supply chain attack targeting South Asian government delivers Shadowpad - Daniel Lunghi
It is possible that the MSI installer could have been modified and then redistributed. However, as it was not publicly available at the time of the incident (September 2022), that would imply that the threat actor retrieved it from a PK gov entity before weaponizing it. #APT
If you are like me and used Twitter to monitor specific keywords with Tweetdeck, just to find out there is no such thing as general keyword search in here, don't /ragequit yet.
AFAIK, you cannot search for a keyword on random users unless you favorited/boosted or have been mentioned in them. Which means you already read them and know about their existence in the first place, which is good for bookmarking, but useless for discovering relevant toots from random users.
However, there is a nice feature in the web advanced view (which you can enable in the "Appearance" preferences):
You get a 3 columns' view, one for notifications, one for your regular timeline, and the last one with the content of your choice: either federated timeline, local timeline, your DMs, etc ...
That's a nice first step, but there is still a lot of space wasted if you have a big screen and resolution.
Here comes the trick I just learned: if you search for a hashtag (let's say, #apt), you get some hashtags results. By clicking on the one you're interested in, it becomes the content of the 3rd column we mentioned before.
Then, if you click on the top-right icon, a "Pin" feature appears. A final click, and tadaaaa, now you have a 4th and permanent column with a hashtag you are interested in !
You can reproduce the same for any hashtag you want and finally have a reason to buy one of those giant screens :)
It does not match the Twitter keyword feature, but it's still nice. It also means that, as a toot writer, it is important to use relevant hashtags.