Our latest report on a CN
#APT targeting tens of governments entities worldwide has been published 🥳 After monitoring it for a long time we realized it is likely related to the recent I-Soon company leaks. It discusses their TTPs and provides lots of IOCs
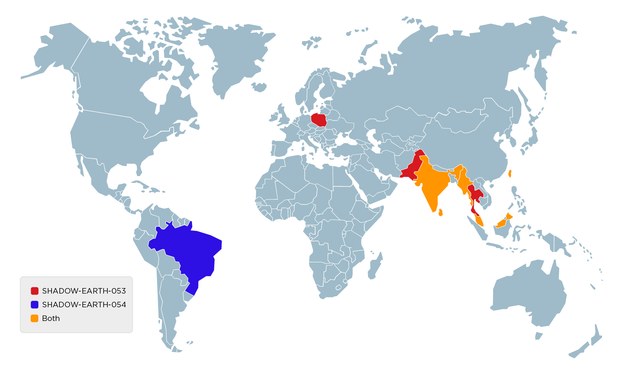
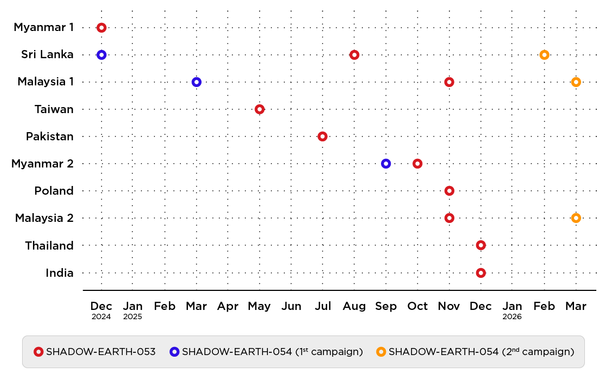
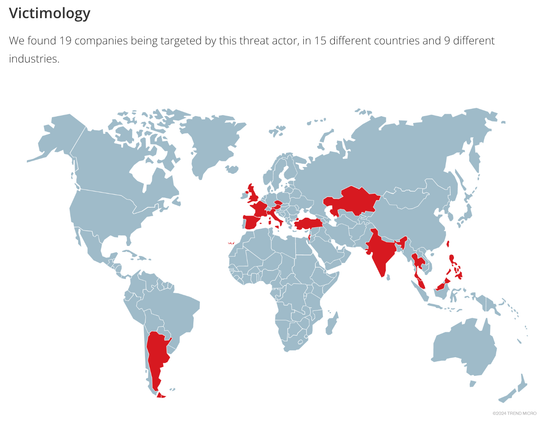
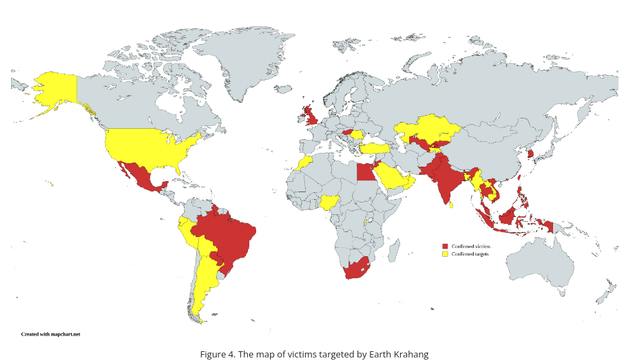
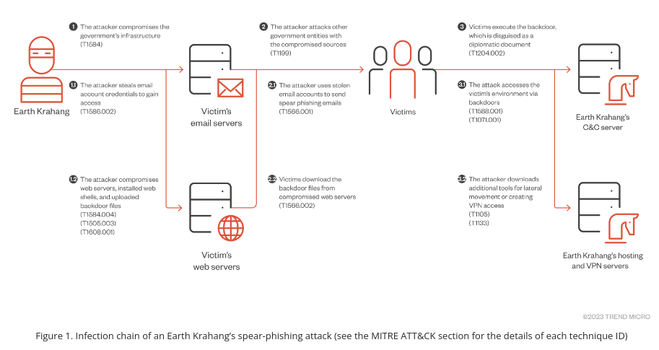
https://trendmicro.com/en_us/research/24/c/earth-krahang.htmlTargets are spread among 5 continents, although some countries are targeted more heavily: one country had 11 of its government entities compromised. Previous victims are used to compromise new ones by abusing their infrastructure to send spear-phishing emails or host malware.
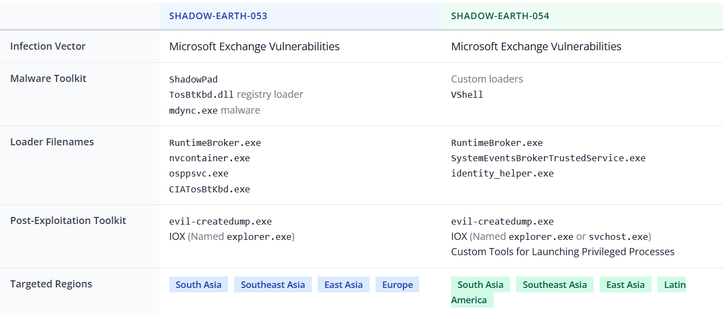
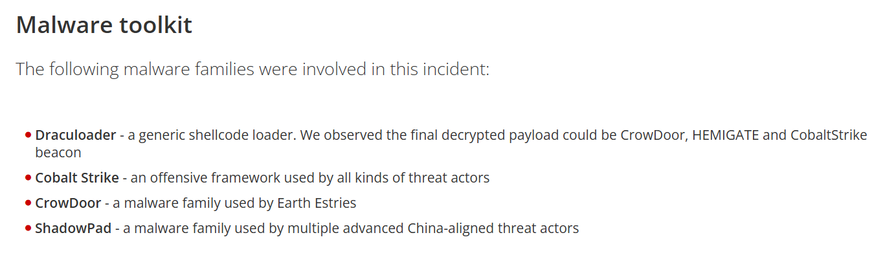
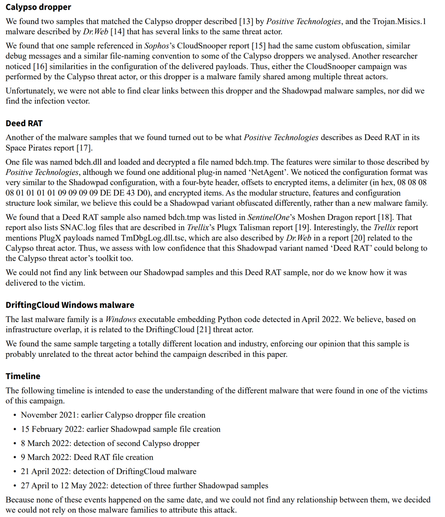
Their favorite malware toolkit are Reshell, a basic .NET backdoor, and Xdealer, also named Dinodas RAT, two custom malwares. They also use the infamous
#CobaltStrike,
#PlugX and
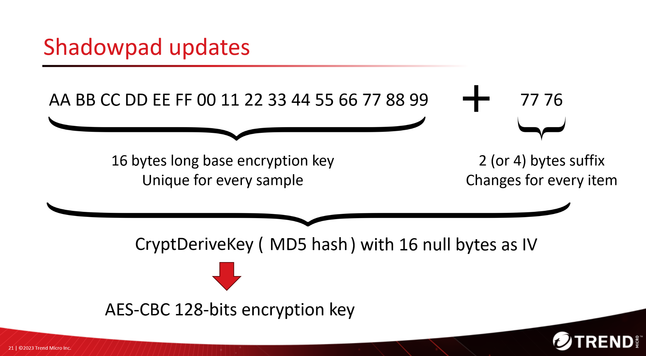
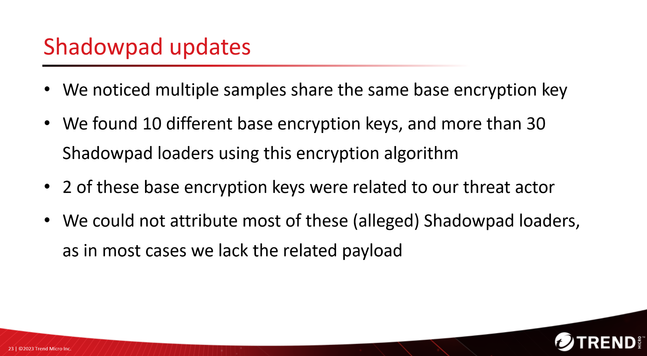
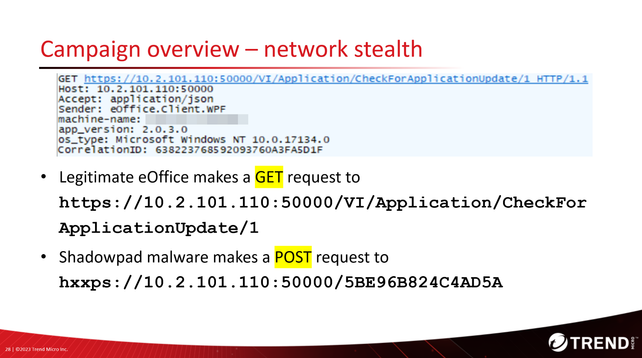
#Shadowpad. Many of their offensive and post-exploitation tools are retrieved from public sources.