#introduction I have been working on targeted attacks for a long time now, first as an incident responder, and now doing threat intelligence at Trend Micro.
I usually focus for a while on a threat actor, and when I feel I know enough, publish something about it. The fun part is that very often, while investigating a threat actor, you end up finding stuff on another one, which you can add to your TODO list once the current investigation is completed :)
BTW, this is a good reason to be careful with the attribution out there, infrastructure overlap and tool sharing are common stuff nowadays.
Some of my previous work on #APT groups:
#Patchwork:
https://www.trendmicro.com/en_us/research/17/l/untangling-the-patchwork-cyberespionage-group.html
#Confucius:
https://www.trendmicro.com/fr_fr/research/18/b/deciphering-confucius-cyberespionage-operations.html
https://www.trendmicro.com/en_us/research/21/h/confucius-uses-pegasus-spyware-related-lures-to-target-pakistani.html
#UrPage/#Bahamut:
https://www.trendmicro.com/en_us/research/18/h/the-urpage-connection-to-bahamut-confucius-and-patchwork.html
A bit of all previous actors:
https://www.first.org/resources/papers/tallinn2019/Linking_South_Asian_cyber_espionnage_groups-to-publish.pdf
#MuddyWater:
https://www.trendmicro.com/en_us/research/18/k/new-powershell-based-backdoor-found-in-turkey-strikingly-similar-to-muddywater-tools.html
https://documents.trendmicro.com/assets/white_papers/wp_new_muddywater_findings_uncovered.pdf
Maybe APT37 (unconfirmed):
https://www.trendmicro.com/en_us/research/19/c/new-slub-backdoor-uses-github-communicates-via-slack.html
#EarthAkhlut/#Tonto:
https://vb2020.vblocalhost.com/uploads/VB2020-Lunghi-Horejsi.pdf
Operation DRBControl:
https://www.trendmicro.com/vinfo/us/security/news/cyber-attacks/operation-drbcontrol-uncovering-a-cyberespionage-campaign-targeting-gambling-companies-in-southeast-asia
#EarthBerberoka:
https://www.trendmicro.com/en_us/research/22/d/new-apt-group-earth-berberoka-targets-gambling-websites-with-old.html
https://www.trendmicro.com/vinfo/us/security/news/cybercrime-and-digital-threats/exposing-earth-berberoka-a-multiplatform-apt-campaign-targeting-online-gambling-sites
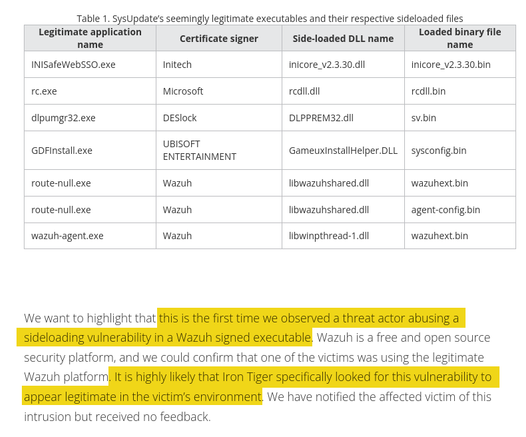
#IronTiger/#EarthSmilodon:
https://www.trendmicro.com/en_no/research/21/d/iron-tiger-apt-updates-toolkit-with-evolved-sysupdate-malware-va.html
https://www.trendmicro.com/en_us/research/22/h/irontiger-compromises-chat-app-Mimi-targets-windows-mac-linux-users.html