| https://twitter.com/thehellu |
Daniel Lunghi
- 268 Followers
- 110 Following
- 19 Posts
@tek In 2019 we wrote something about them. Don't ask me why but it seems the link to our research is dead now, but you can find it here https://web.archive.org/web/20190719200241/https://blog.trendmicro.com/trendlabs-security-intelligence/spam-campaign-targets-colombian-entities-with-custom-proyecto-rat-email-service-yopmail-for-cc/
At the time, we stated the following: "Our findings indicate that the campaign appears to be the work of a group involved in business email compromise (BEC) or cybercrime, and unlikely to be an advanced persistent threat (APT)."
Part of this assessment comes from the targeted verticals: "Notably, we noticed that multiple employee savings funds (called “Fondo de empleados” in Colombia) were targeted. These entities barely have access to sensitive information, but they are likely to possess a reasonable amount of money."
I have not followed the group then (only a quick follow up in 2021 https://www.trendmicro.com/en_us/research/21/i/apt-c-36-updates-its-long-term-spam-campaign-against-south-ameri.html )
We did not perform incident response on this, so we could still be wrong. Hope this helps
Spam Campaign Targets Colombian Entities with Custom-made ‘Proyecto RAT,’ Uses Email Service YOPmail for C&C - TrendLabs Security Intelligence Blog
We observed a recent campaign that primarily targets financial institutions and governmental organizations in the South American region, particularly in Colombia. This blog post covers the activities we observed, the remote access tools (RATs) used, the campaign's techniques and procedures, and its indicators of compromise (IoCs). Our findings indicate that the campaign appears to be the work of a group involved in business email compromise (BEC) or cybercrime, and unlikely to be an advanced persistent threat (APT).
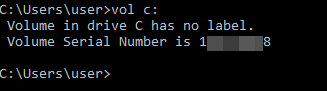
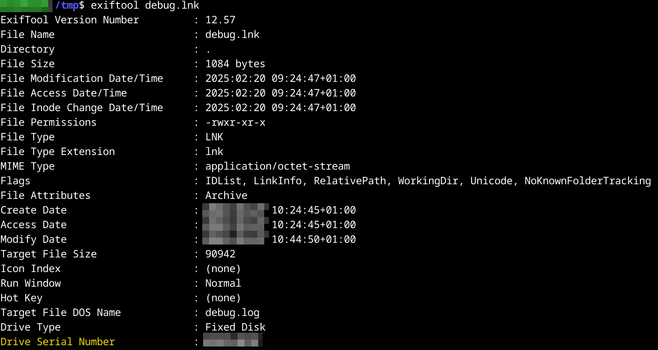
You can then use the VolumeID tool from Sysinternals to change the volume serial number of your virtual machine
https://learn.microsoft.com/en-us/sysinternals/downloads/volumeid
#APT
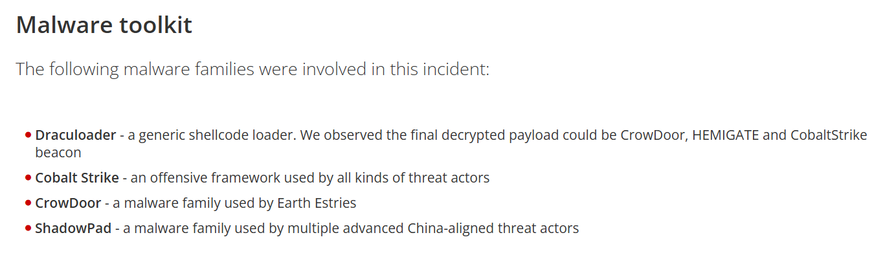
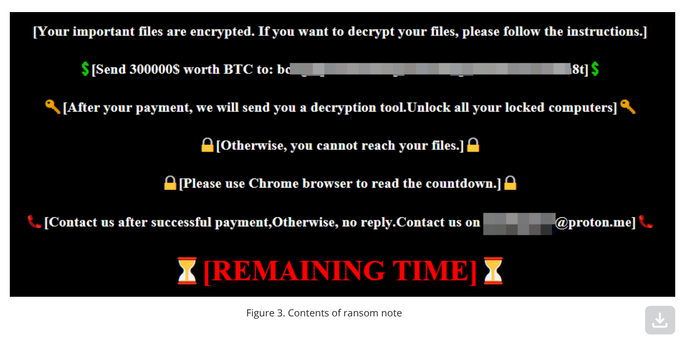
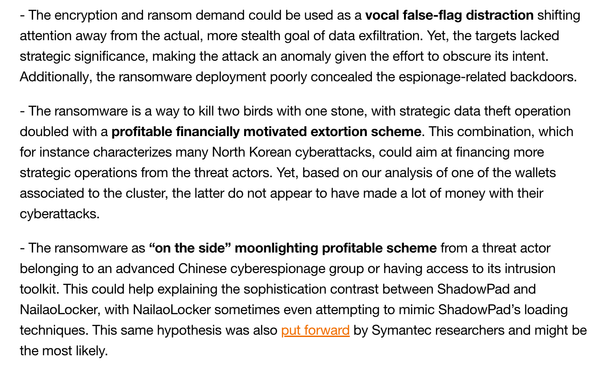
Orange Cyberdefense saw the same threat and named the ransomware "NailaoLocker" https://www.orangecyberdefense.com/global/blog/cert-news/meet-nailaolocker-a-ransomware-distributed-in-europe-by-shadowpad-and-plugx-backdoors They share interesting thoughts on the motivations of the ransomware deployment, although they don't have the final answer. We also saw no financial gain for the threat actor
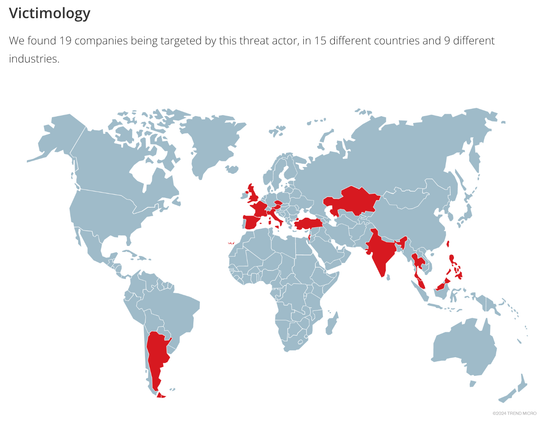
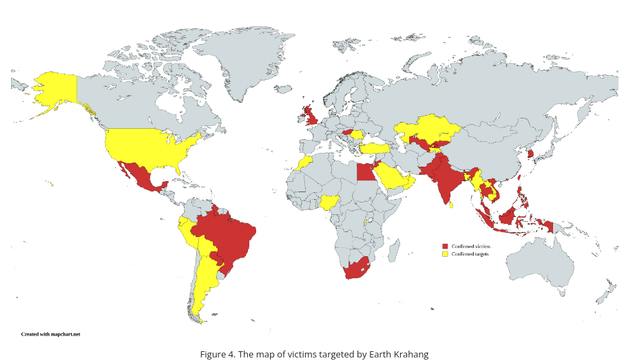
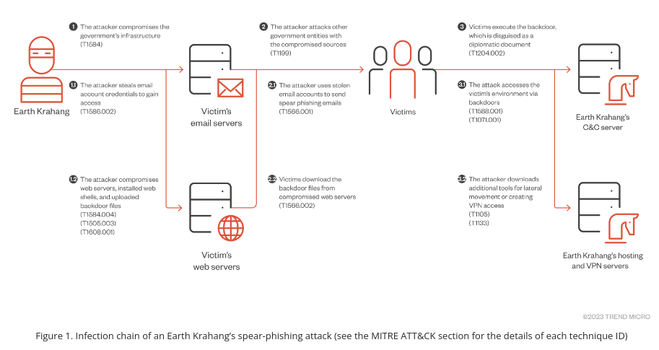
Targets are spread among 5 continents, although some countries are targeted more heavily: one country had 11 of its government entities compromised. Previous victims are used to compromise new ones by abusing their infrastructure to send spear-phishing emails or host malware.
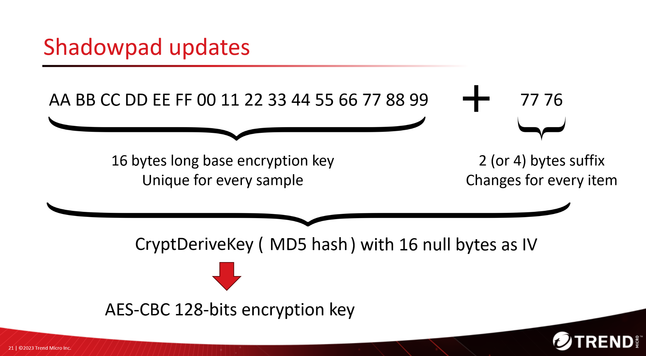
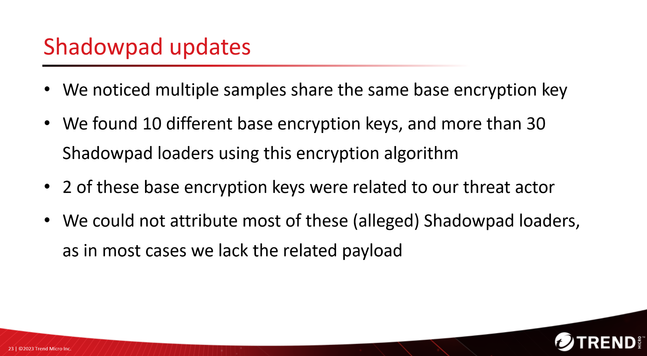
Their favorite malware toolkit are Reshell, a basic .NET backdoor, and Xdealer, also named Dinodas RAT, two custom malwares. They also use the infamous #CobaltStrike, #PlugX and #Shadowpad. Many of their offensive and post-exploitation tools are retrieved from public sources.
The slides https://virusbulletin.com/uploads/pdf/conference/vb2023/slides/Slides-Possible-supply-chain-attack-targeting-South-Asian-government-delivers-Shadowpad.pdf and paper https://virusbulletin.com/uploads/pdf/conference/vb2023/papers/Possible-supply-chain-attack-targeting-South-Asian-government-delivers-Shadowpad.pdf are also available. In addition to what we published in July in our blog, the paper details our failed attempts to attribute this attack based on custom malware families and their links to other advanced threat actors #threatintel
Possible supply chain attack targeting South Asian government delivers Shadowpad - Daniel Lunghi
It is possible that the MSI installer could have been modified and then redistributed. However, as it was not publicly available at the time of the incident (September 2022), that would imply that the threat actor retrieved it from a PK gov entity before weaponizing it. #APT