:antifa:🇪🇺🇺🇦💚
Sei ein Mensch.
Nerd.
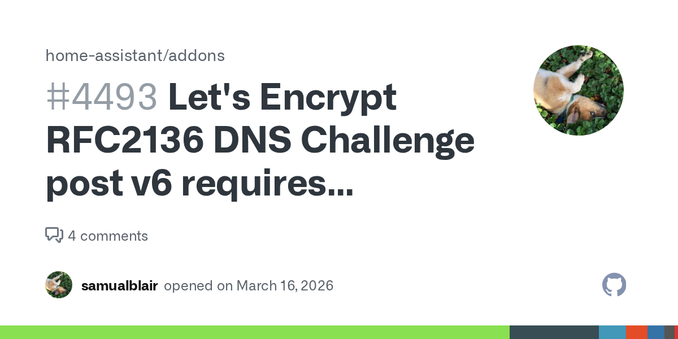
try stuff, break stuff, fix stuff.
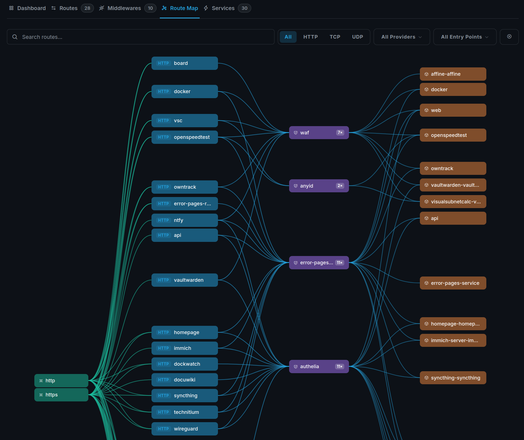
mostly DBA, but doing a lot more, Linux, docker, kubernetes, virtualization, storage, network.
| github | https://github.com/stelb/ |
| https://www.linkedin.com/in/stefanlebreton | |
| Pixelfed | https://pixelfed.social/stelb |
| Forgejo | https://forgejo.anyops.de/AnyOps |